Complete control over your cyber asset attack surface

Secure Networks with Enhanced Vulnerability Insights
Monitor user behaviors, group permissions, and asset configurations to proactively identify and address vulnerabilities, thereby strengthening your network's defense.
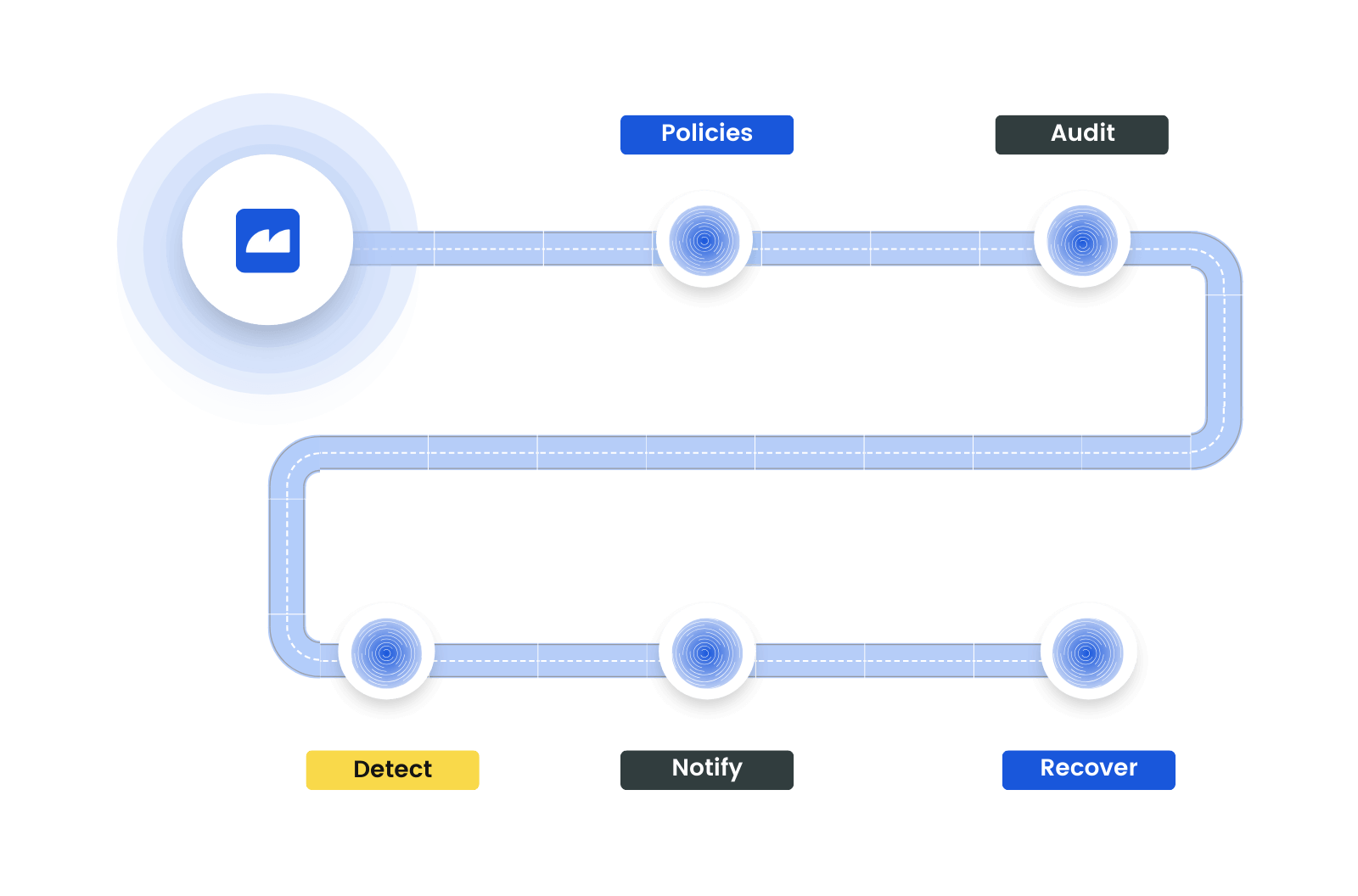
Automate Security Audits
Maintain high standards of compliance by closely aligning Tenable's data with your security policies. Ensure that user groups and scan procedures meet your security criteria, contributing to a more secure and compliant organizational environment.
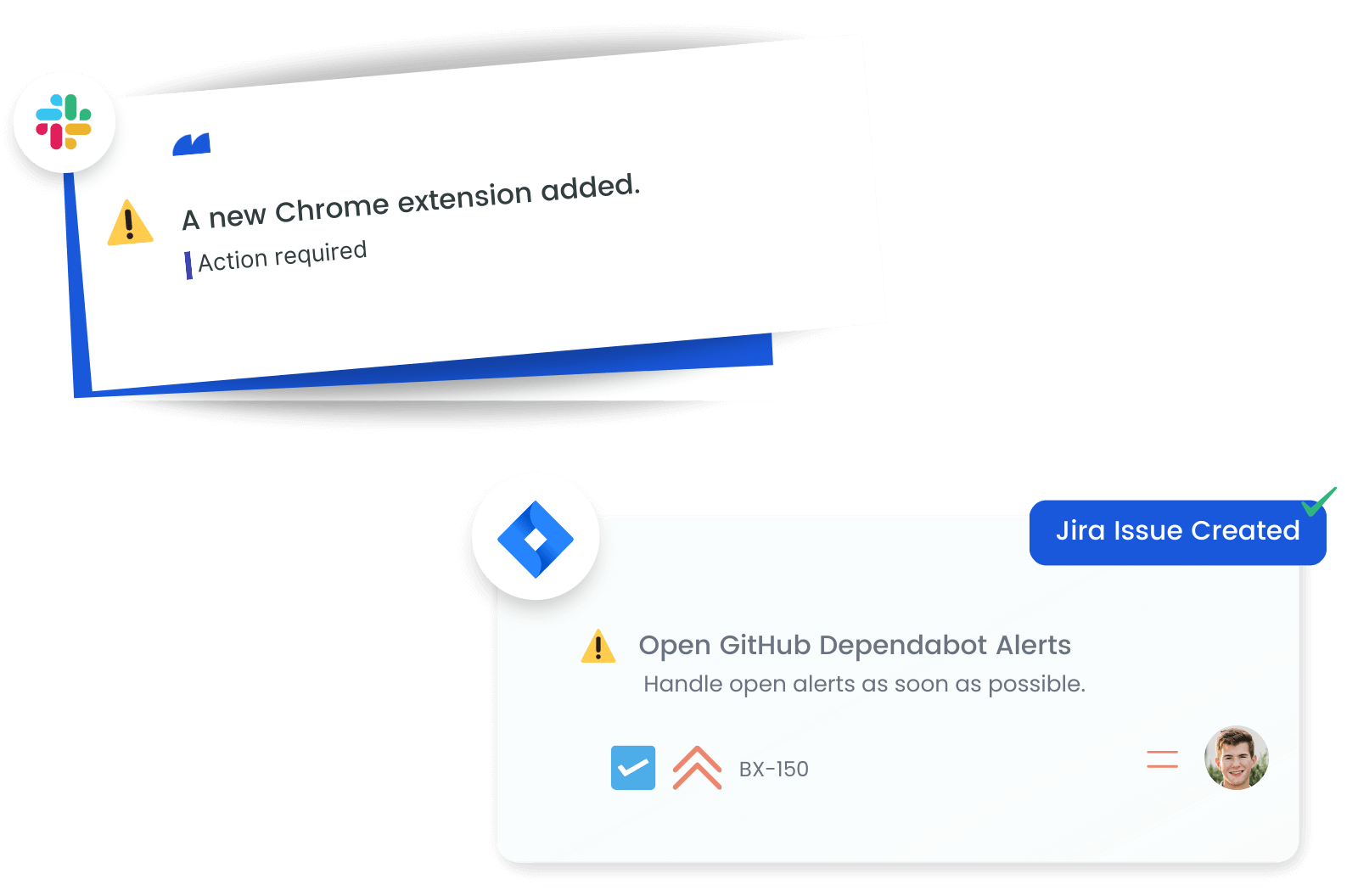
Enable Quick Response to Changes and Threats
Empower your security team with the ability to respond swiftly to changes in the Tenable environment. Immediate alerts on user changes, scan updates, and vulnerability detections enable a rapid response, crucial for minimizing potential security breaches.
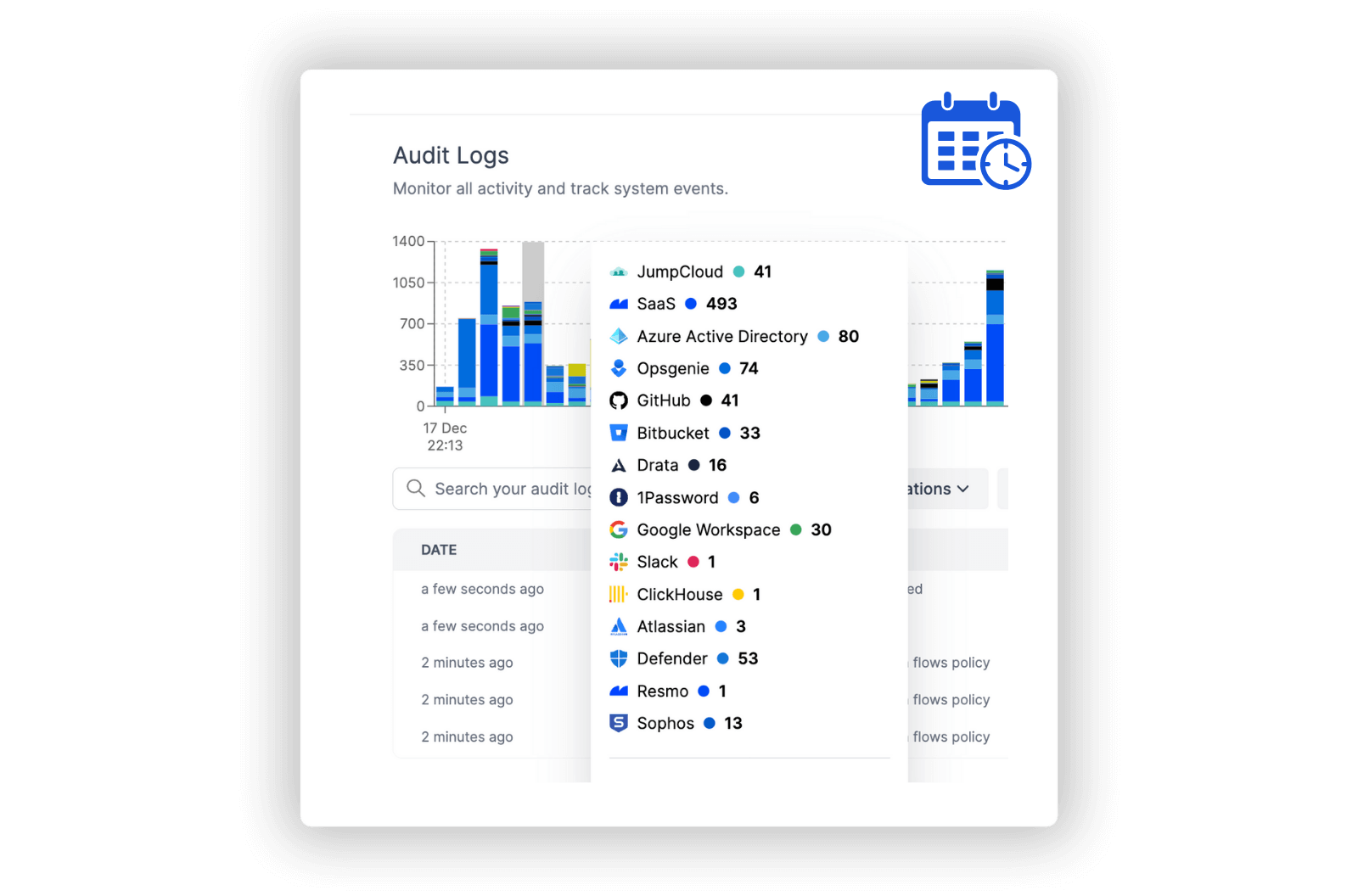
Streamline Incident Investigations
Build a stronger security posture by conducting in-depth audits of Tenable activities. A thorough analysis of vulnerabilities, scans, and user behavior provides valuable insights, enhancing your organization’s ability to respond to and mitigate security risks.
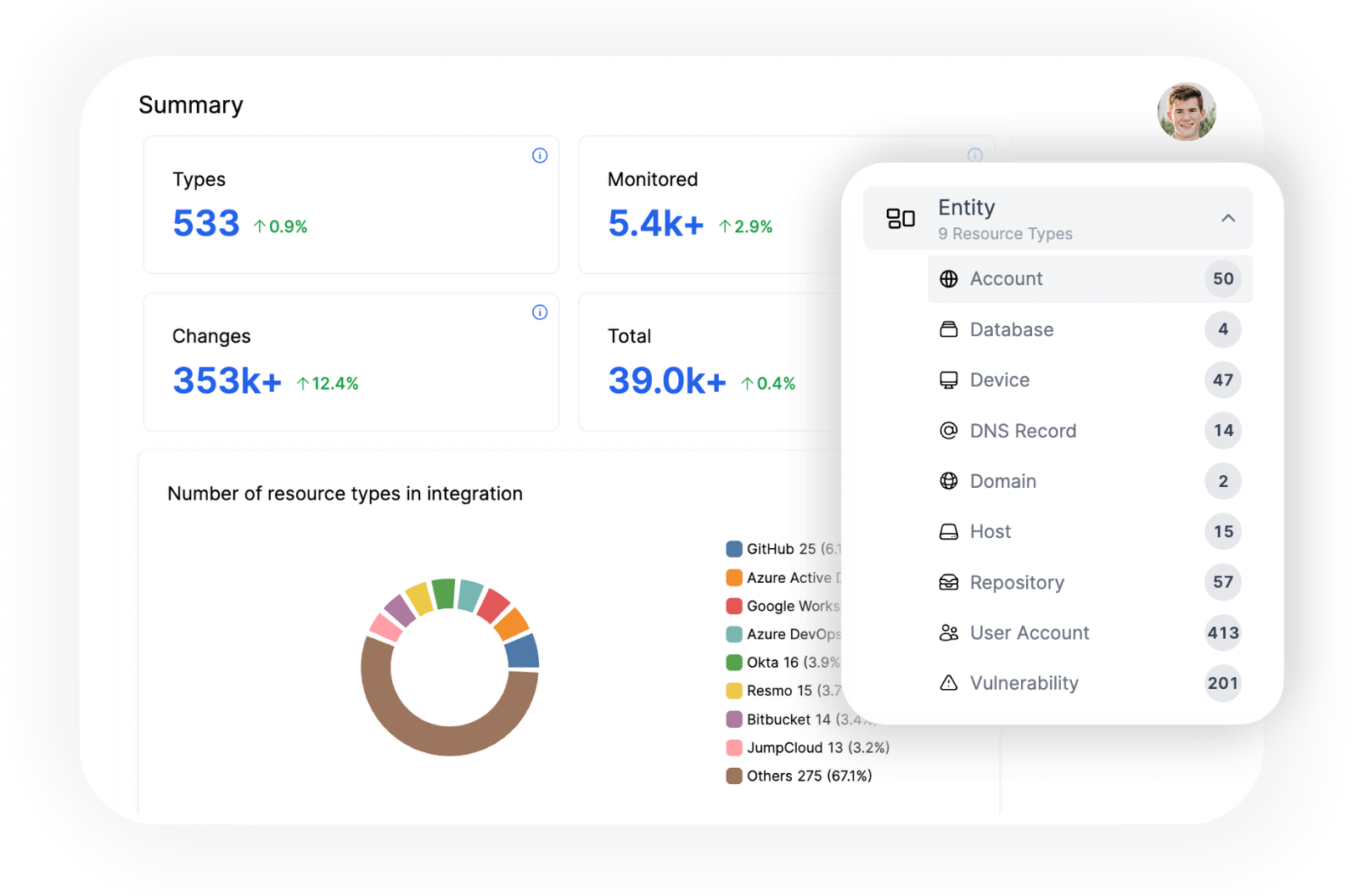
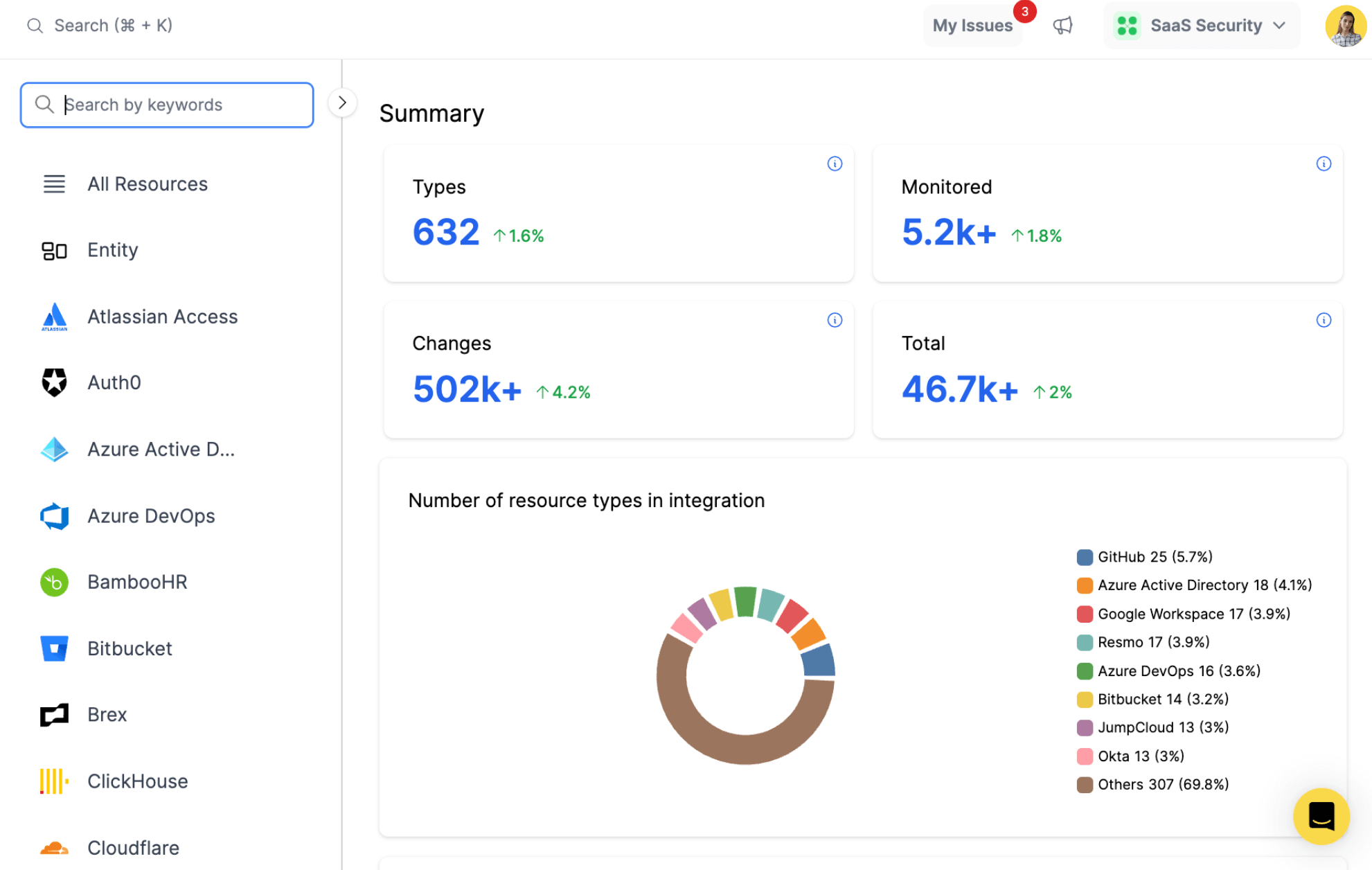
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- Asset
- Image
- Scan
- Permission
- User
- Vulnerability
- WAS Scan
- And more
Tenable Integration with Resmo
Tenable is a cloud-based vulnerability management platform that allows organizations to identify, assess, and remediate security risks across their IT infrastructure. It provides comprehensive vulnerability scanning and assessment capabilities, helping organizations proactively manage their security posture.
Resmo's integration with Tenable provides valuable insights into user management, vulnerability assessments, and asset configurations. By accessing user details, group settings, vulnerability scan properties, and asset configurations, organizations can optimize their vulnerability management and enhance security measures.
Key features:
- Review the details of users, their associated groups, and permissions.
- Examine how user groups are configured, including their permissions and user counts.
- Analyze the properties of vulnerability scans, including schedules and progress.
- Identify the details of detected vulnerabilities, including severity and affected assets.
- Access asset configurations, including IP addresses, hostnames, and installed software.
Secure your growth. Know what is happening on SaaS and Cloud.









