Continuously safeguard your JumpCloud resources

Optimize User and Device Management
Keep track of your organization's user and device management with JumpCloud. Monitoring user activities, device assignments, and group memberships helps optimize user management and device utilization.
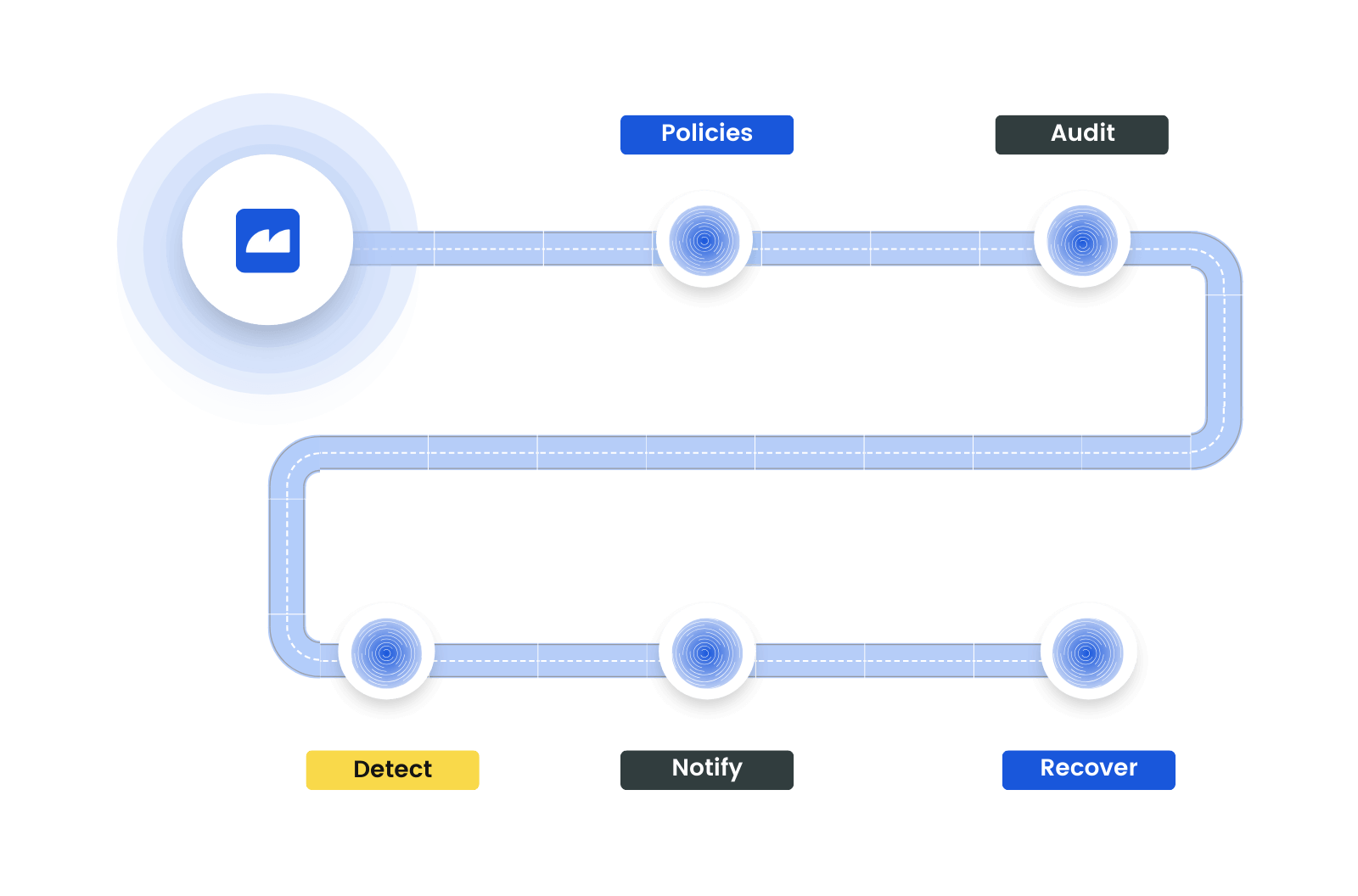
Reinforce Security with Automated Policies
Automate risk assessments with policies to ensure secure user access control and authentication. These policies play a crucial role in safeguarding your organizational data and resources.
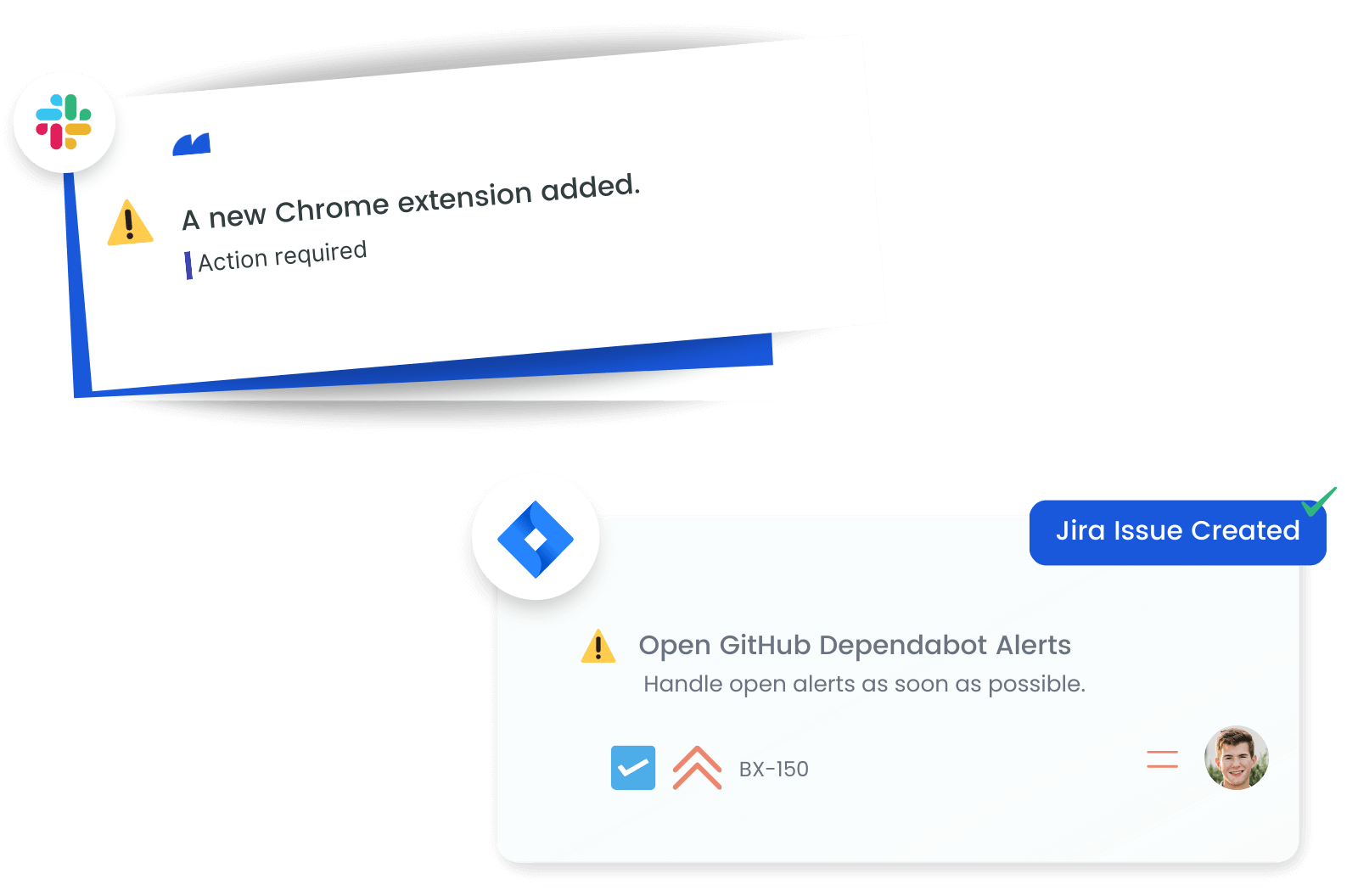
Maintain Security with Real-Time Alerts
Receive immediate updates on crucial changes in user management and security policies. Alerts for new users or groups, device configuration updates, or policy changes help maintain a secure and efficient user management environment.
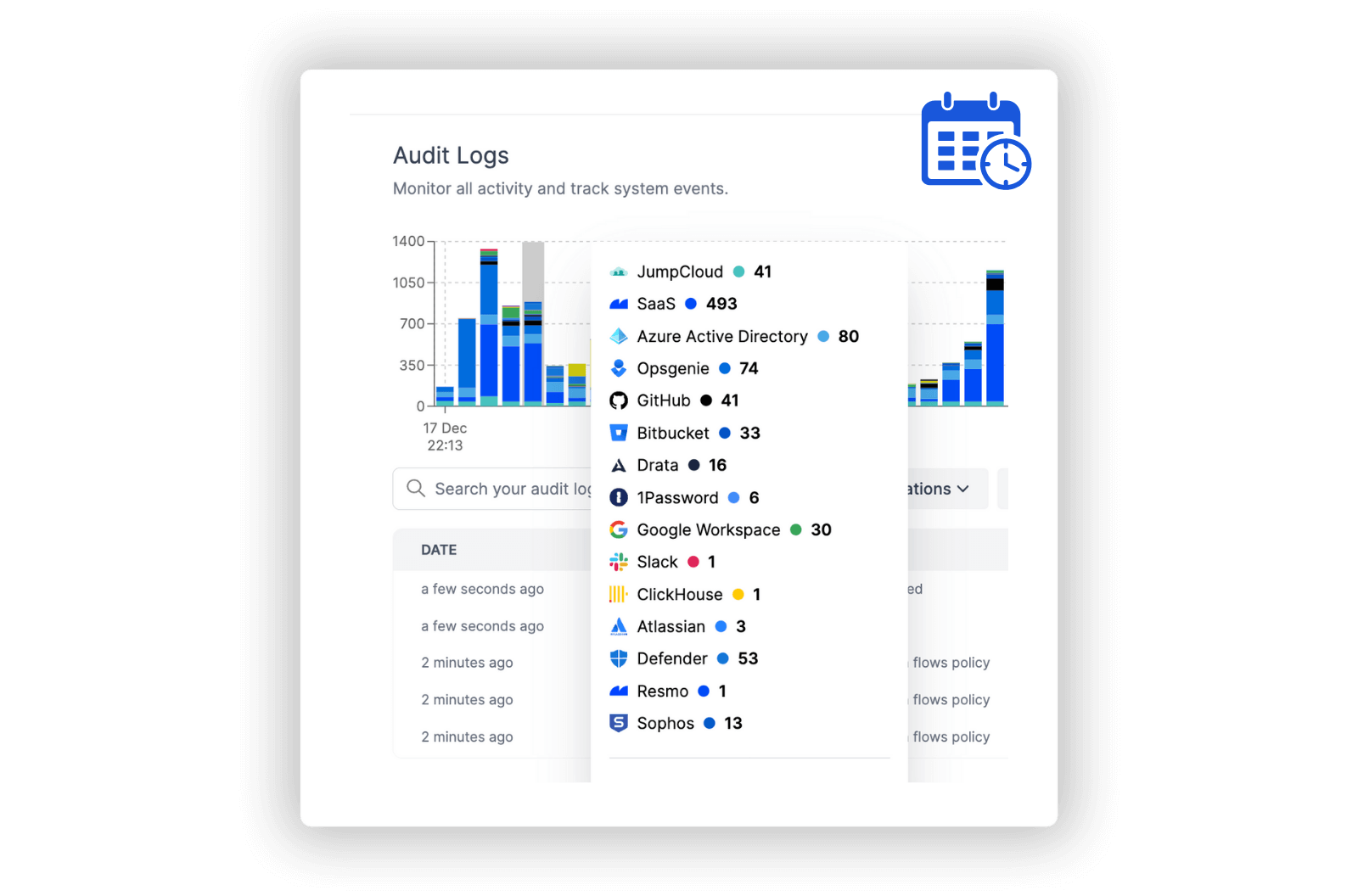
Investigate Anomalies in Detail
Utilize detailed logs from JumpCloud for a comprehensive view of user and device activities. This information is key in enhancing security measures and making informed decisions about resource and user management.
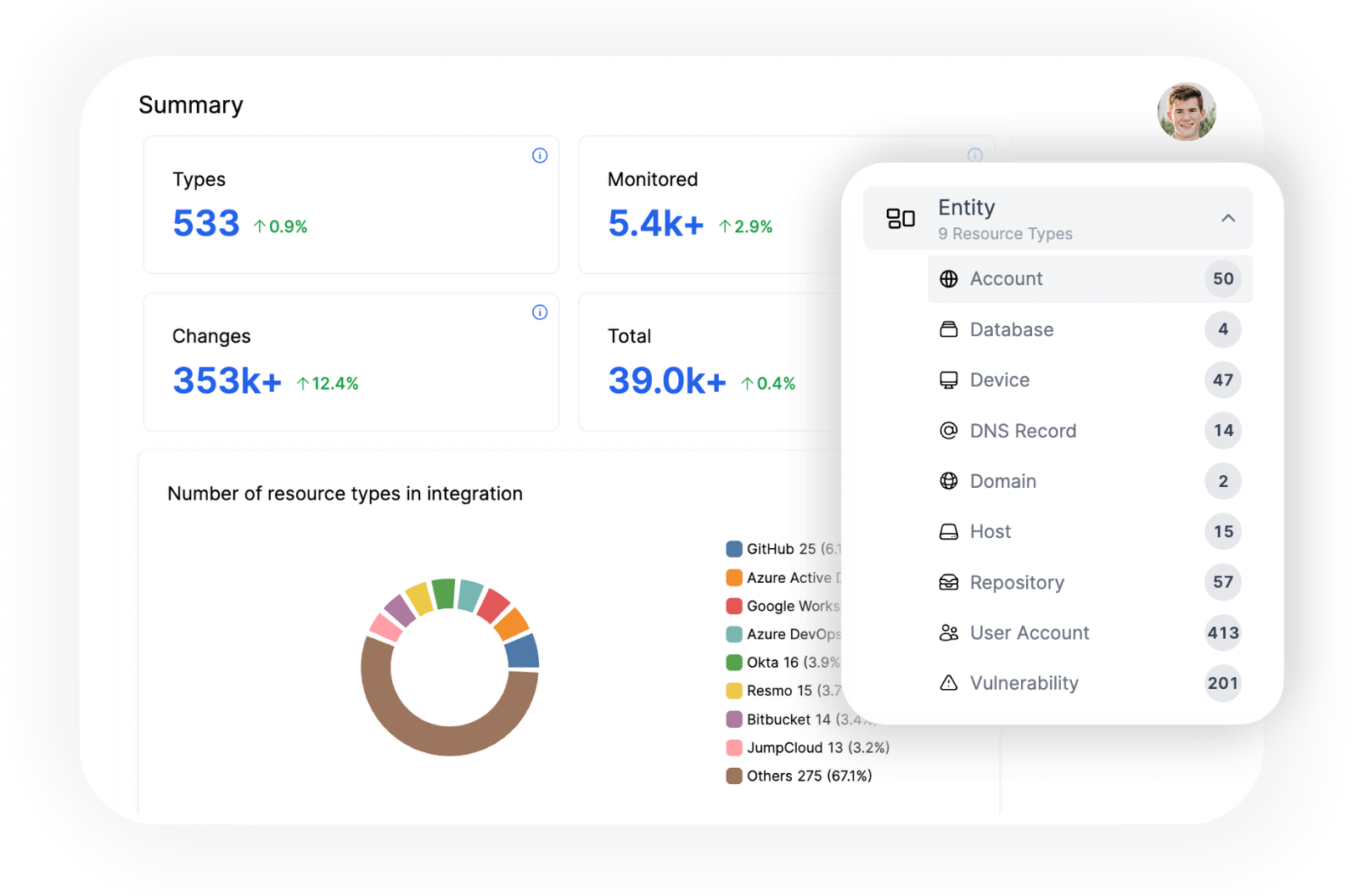
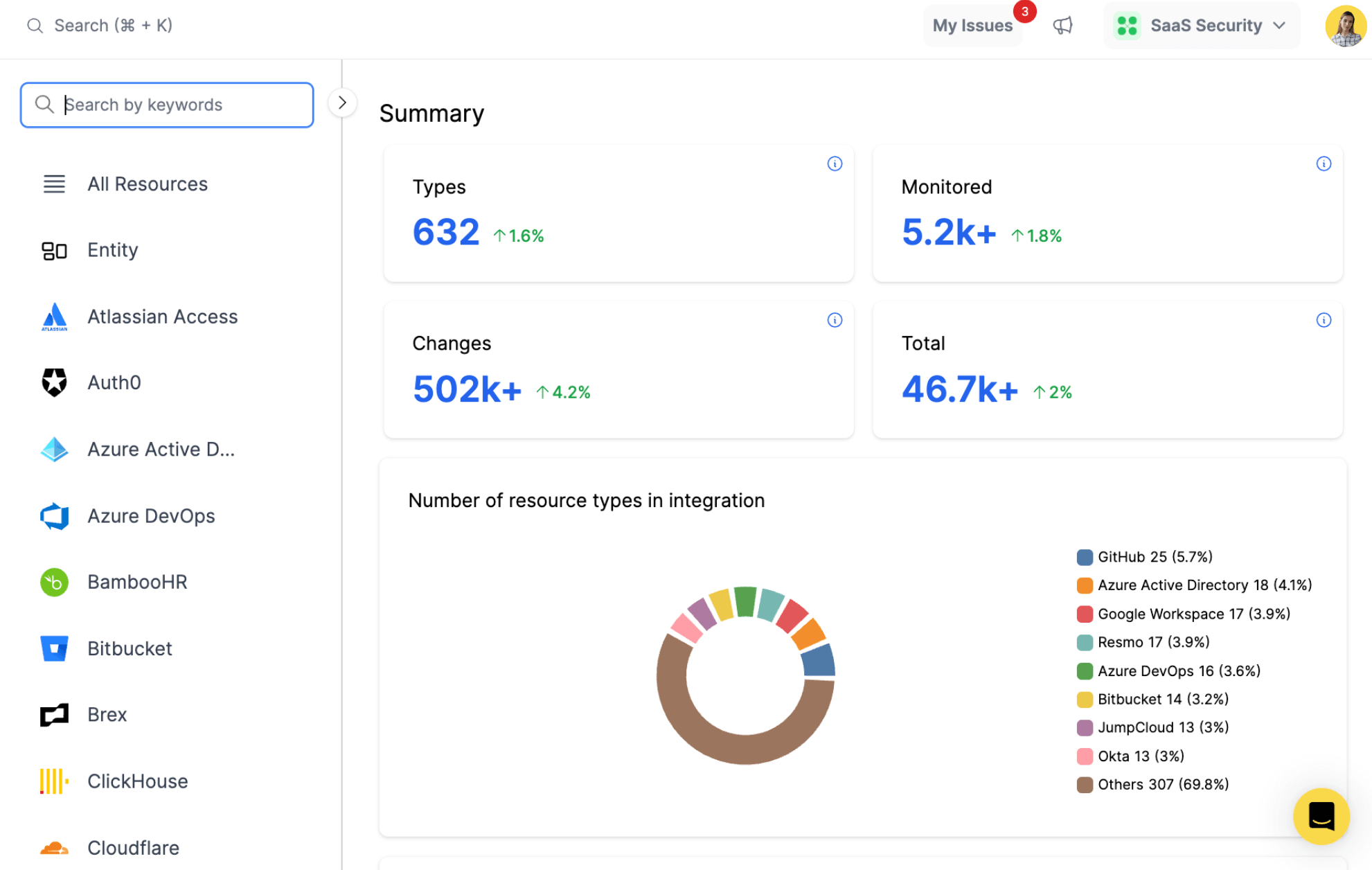
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- Apple MDM
- Application
- Authentication Policy
- Device
- Device Group
- Directory
- IP List
- Organization
- Policy
- User
- And more
Elevate JumpCloud Security and Access Management with Resmo
JumpCloud is a cloud-based directory service that helps organizations manage user identities and their access to resources, including devices, applications, file servers, and networks. It provides a comprehensive platform for user and device management, making it easier for IT teams to enforce policies and secure their environment.
Resmo's integration with JumpCloud can bring significant value in managing and securing an organization's IT environment. By providing visibility into active users, device configurations, authentication policies, integrated applications, and directory settings.
Key features:
- Count the number of active users, devices, and user groups within the organization.
- Identify devices assigned to specific users and understand their configurations.
- Determine the current authentication policies in place and how they affect user access.
- Measure the number of applications integrated with JumpCloud and identify user groups with access to them.
- Examine the IP lists, directory configurations, and device groups used within the organization.
Secure your growth. Know what is happening on SaaS and Cloud.









