Monitor Atlassian configurations and changes in one place

Manage User Access Securely
Track user access details within Atlassian Access to enhance security. Understanding who has access to various tools and their roles is crucial for maintaining secure and efficient team operations.
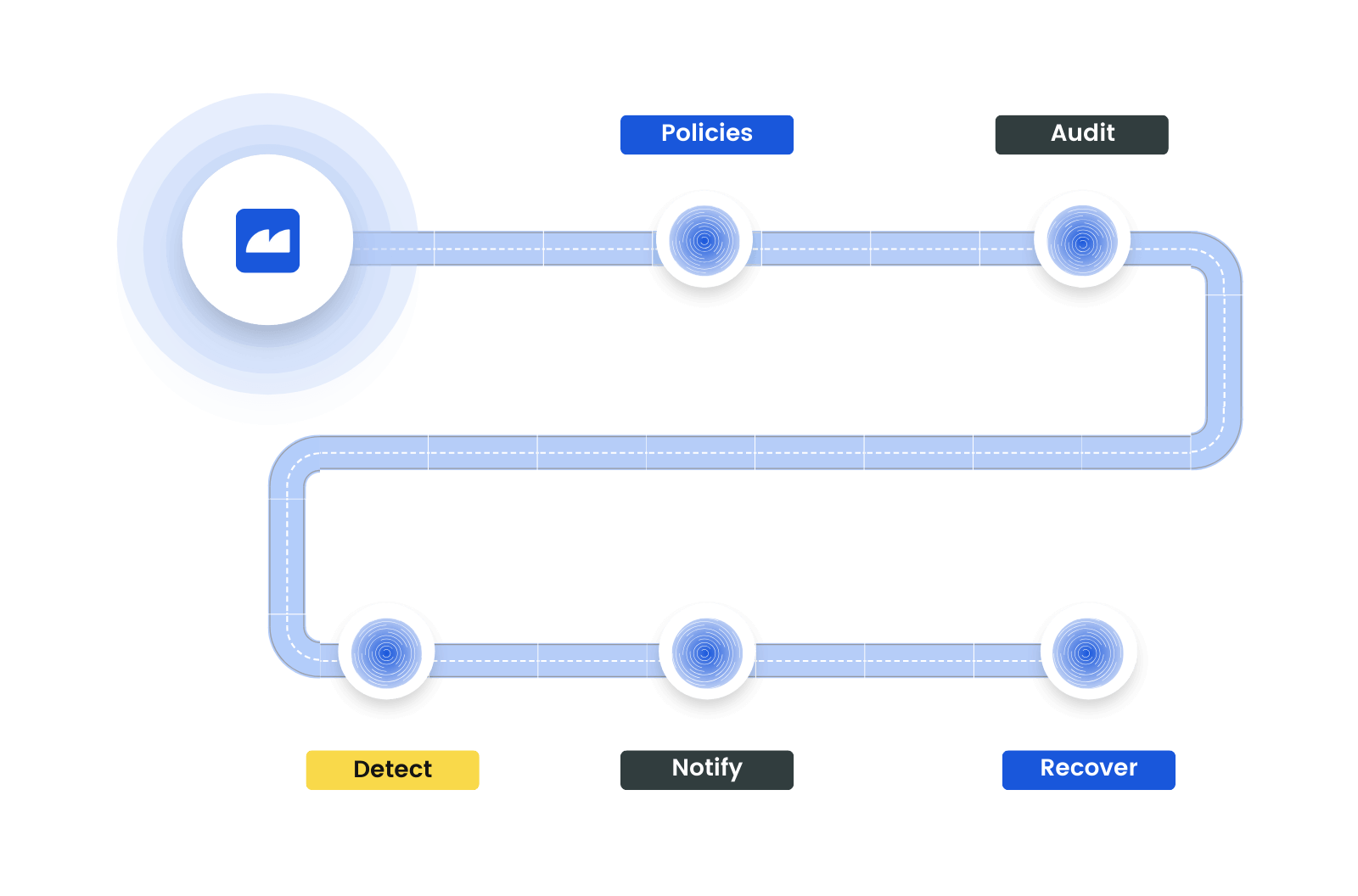
Automate Vulnerability and Change Assessment
Implement and enforce automated policies for vulnerability and change assessments. Continuously identify and address security risks, maintaining compliance with industry standards.
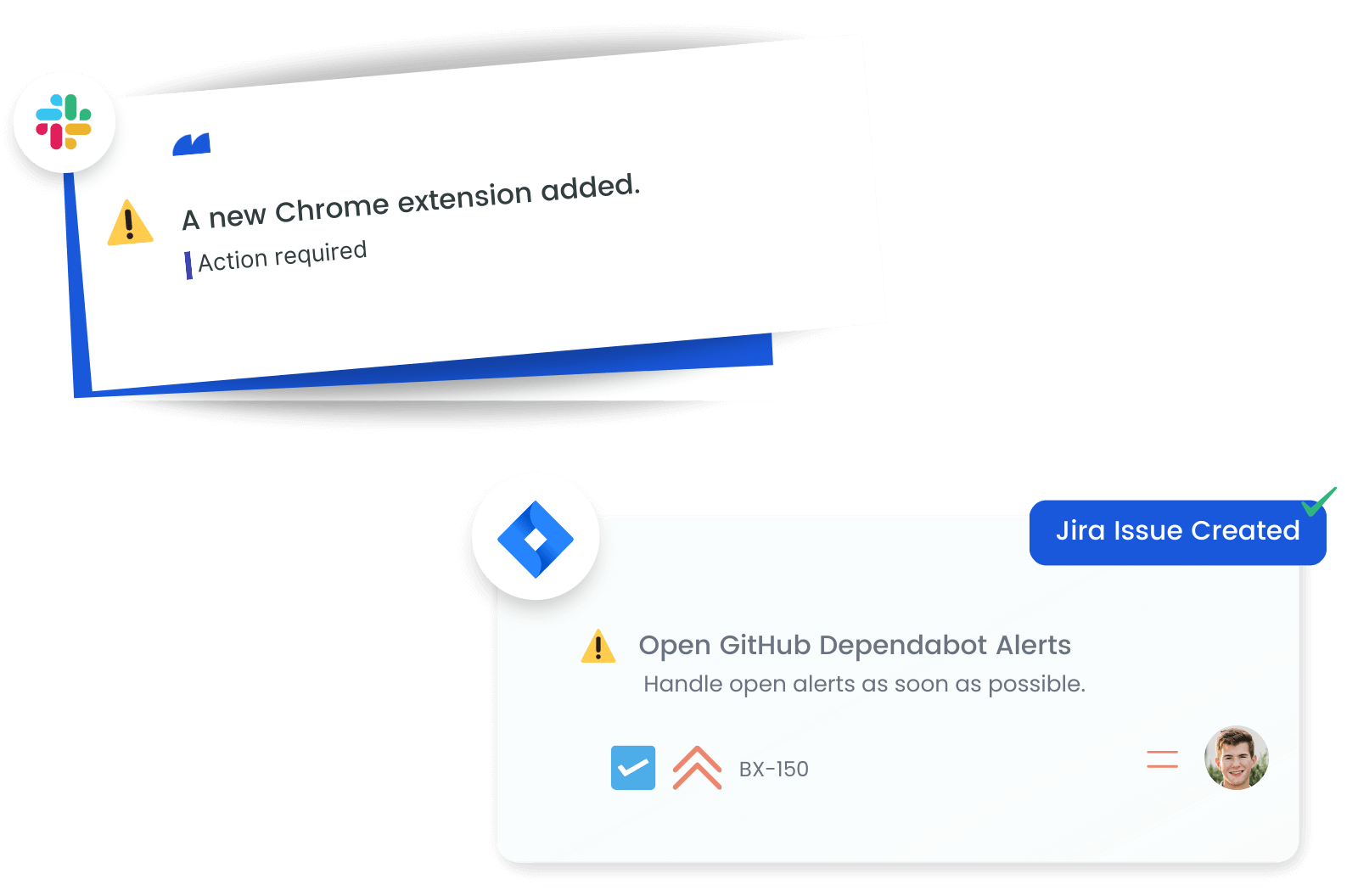
Stay Updated on Critical Changes
Configure alerts to get instant notifications on important changes within Atlassian. Whether it's a new user addition or a change in access permissions, staying informed enables quick action to safeguard your digital environment.
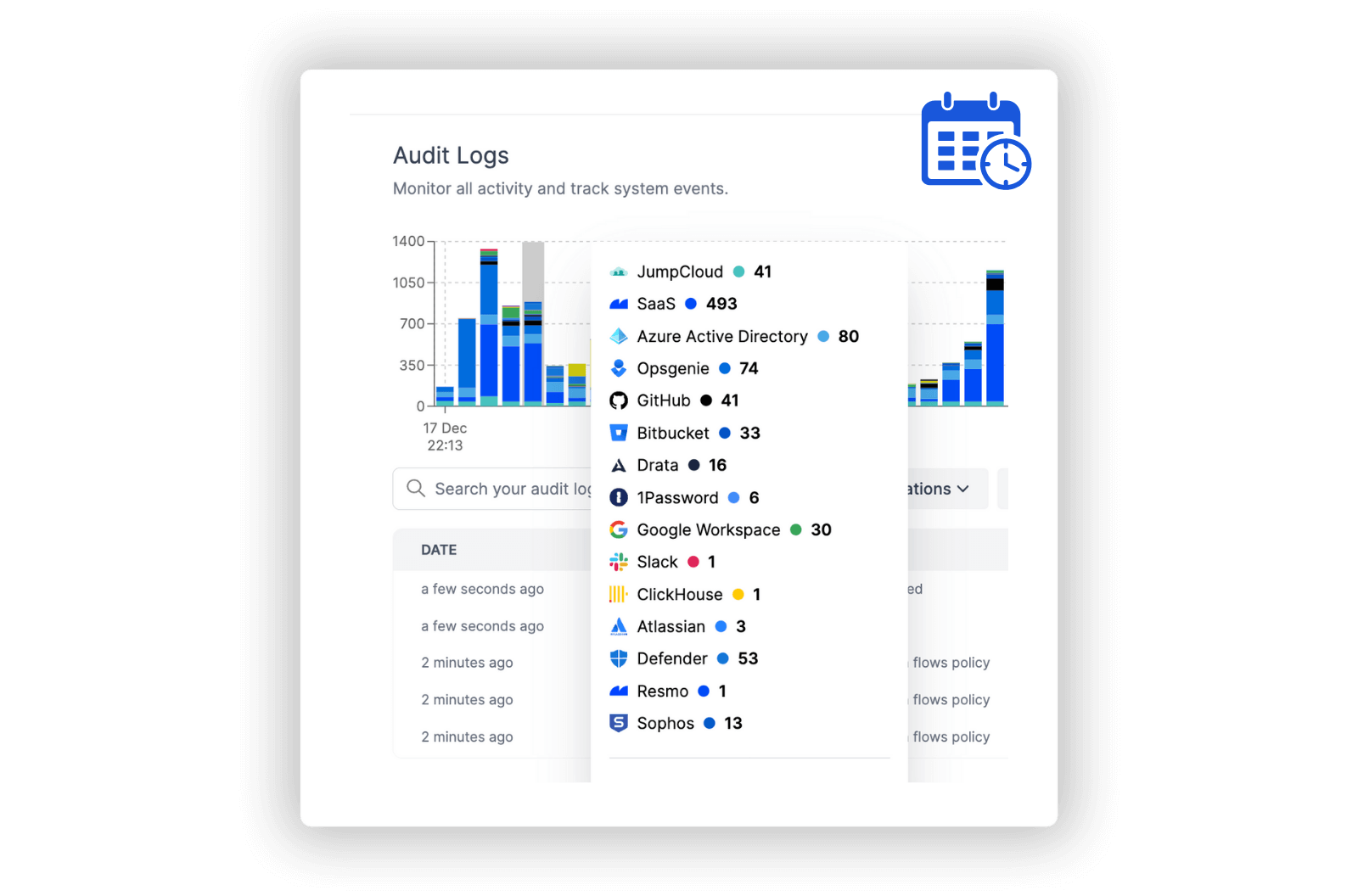
Track and Review Access Changes
Maintain comprehensive audit logs of all activities in Atlassian. Reviewing these logs helps in understanding access patterns, policy effectiveness, and detecting any unusual activity, contributing to a stronger security strategy.
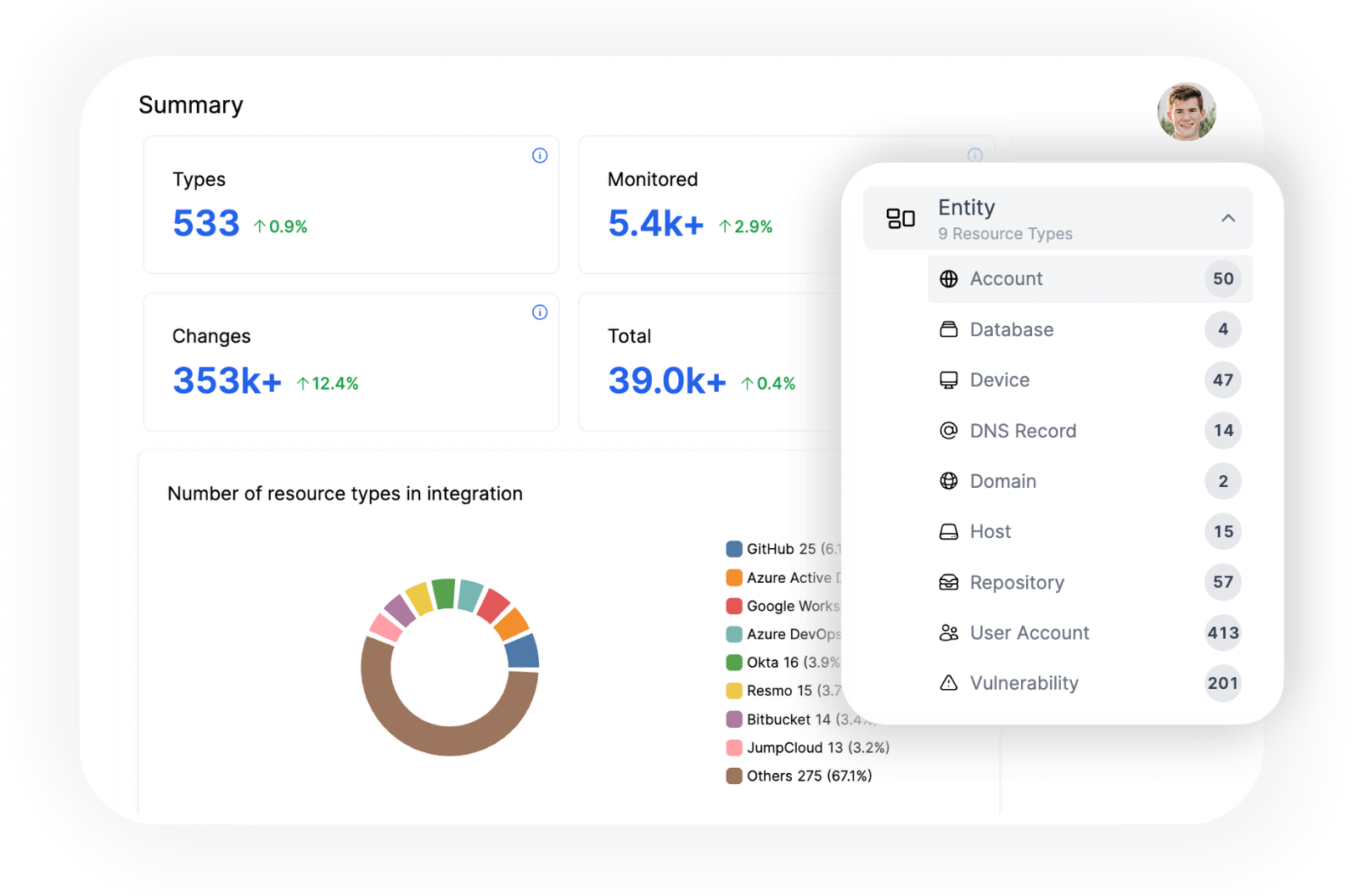
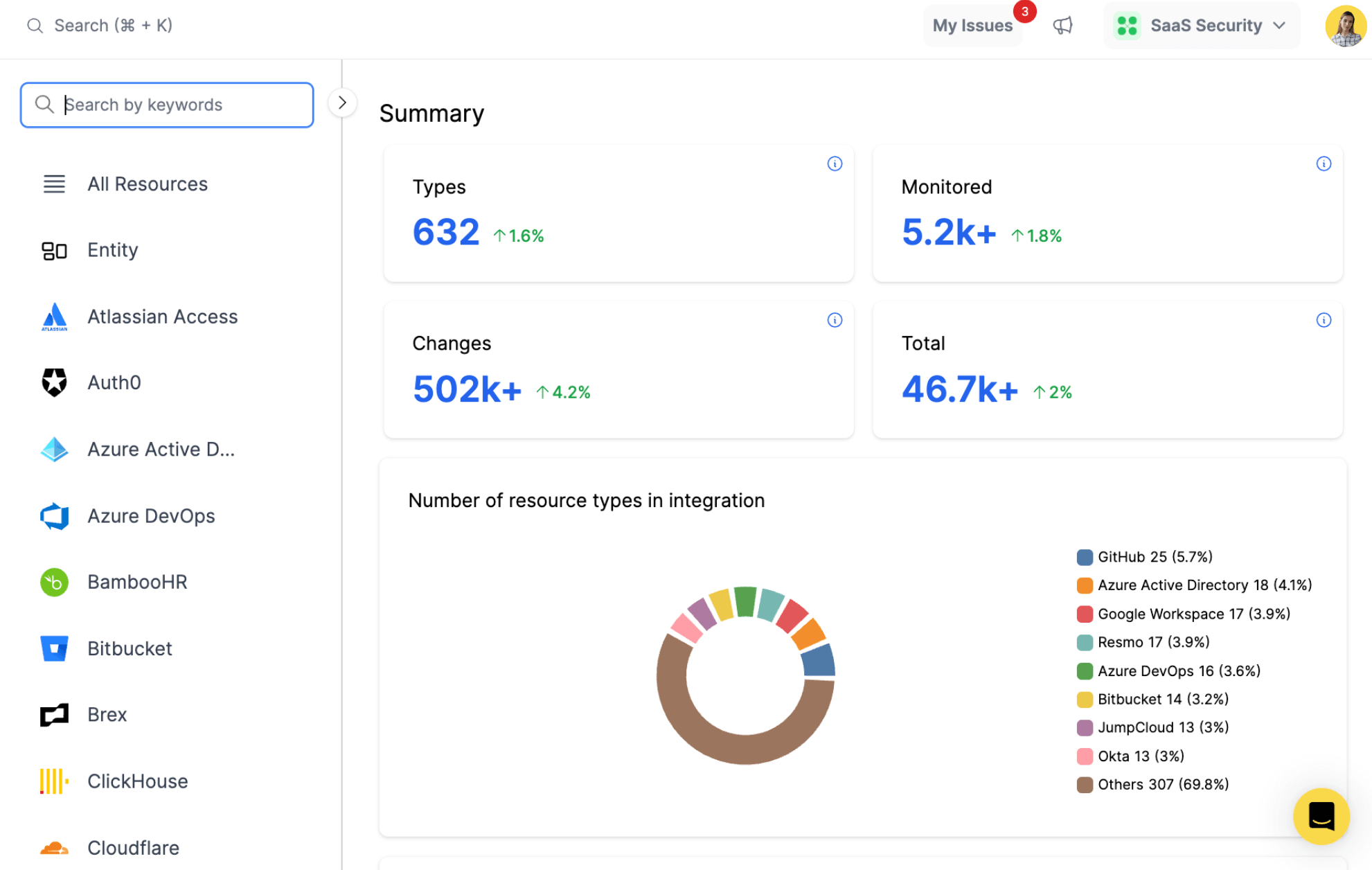
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- Domain
- User
- Organization
- Policy
- Workspace
Atlassian Integration with Resmo
Atlassian is a cloud-based subscription service that provides enhanced security and centralized administration across all Atlassian cloud products. It offers features like SAML single sign-on, user provisioning, and audit logs, enabling organizations to manage their users and enforce security policies across all Atlassian cloud services.
Resmo's integration with Atlassian provides deep insights into user access, workspace distribution, policy enforcement, and role assignments. This can help organizations to enforce better security controls, effectively manage their Atlassian resources, and understand user responsibilities, leading to an enhanced security posture and more efficient use of Atlassian products.
Key features:
- Count the number of users who have access to an Atlassian product.
- Identify the workspaces that exist in the organization.
- Determine the policies applied to the organization.
- Understand the roles and responsibilities of each user
Secure your growth. Know what is happening on SaaS and Cloud.









