Enhance your IAM through complete asset visibility and security

Streamline User Management
Monitor detailed information about each user in MonoSign, including their linked applications, groups, and permissions. Understanding these aspects helps in optimizing identity and access management, ensuring users have appropriate access rights.
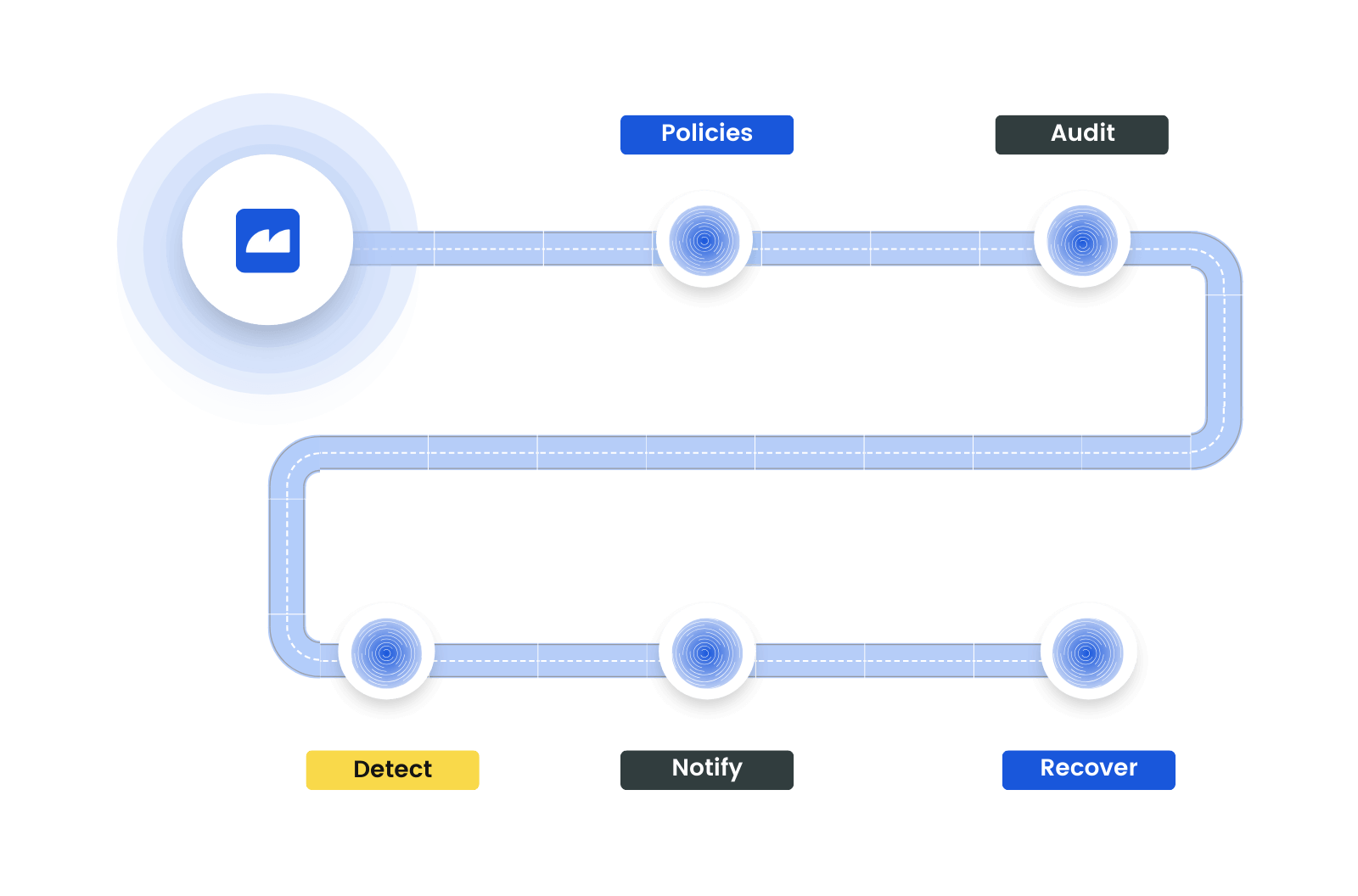
Enhance Security and Authentication
Implement policies for regularly auditing user passwords, authenticators, and roles within MonoSign. This approach is essential for maintaining robust security practices, ensuring strong password policies, and managing authentication methods effectively.
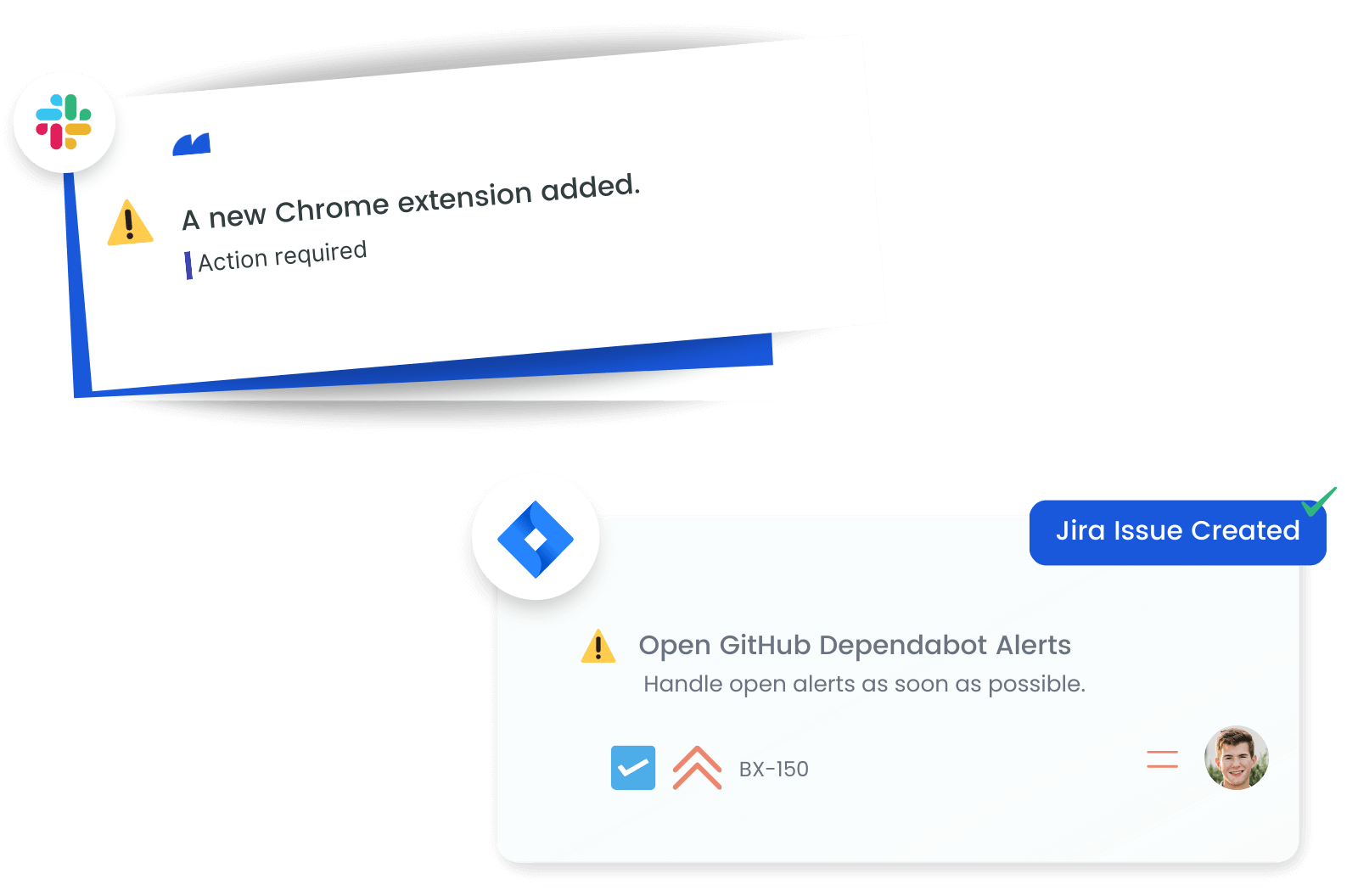
Receive Notifications on User Changes
Set up alerts to stay informed about significant updates in your MonoSign environment. Be notified of changes in user profiles, permission modifications, or updates to authenticators and roles. These alerts enable prompt action to address any potential security issues.
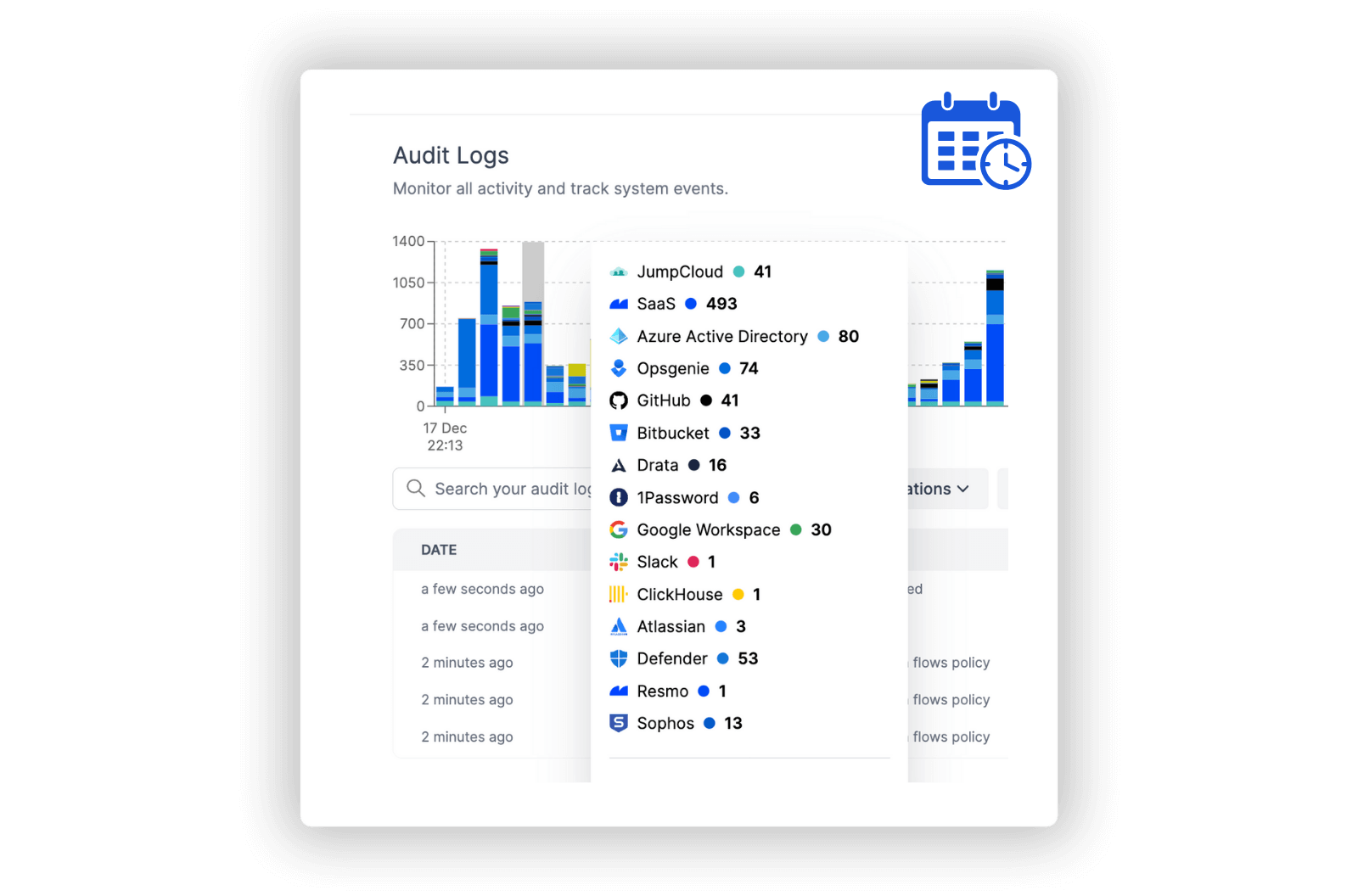
Track of Access and Permissions
Maintain comprehensive logs of user activities, password changes, and permission updates in MonoSign. Regular review of these logs provides insights into user behavior, access management, and adherence to security protocols, aiding in the continuous improvement of your identity management system.
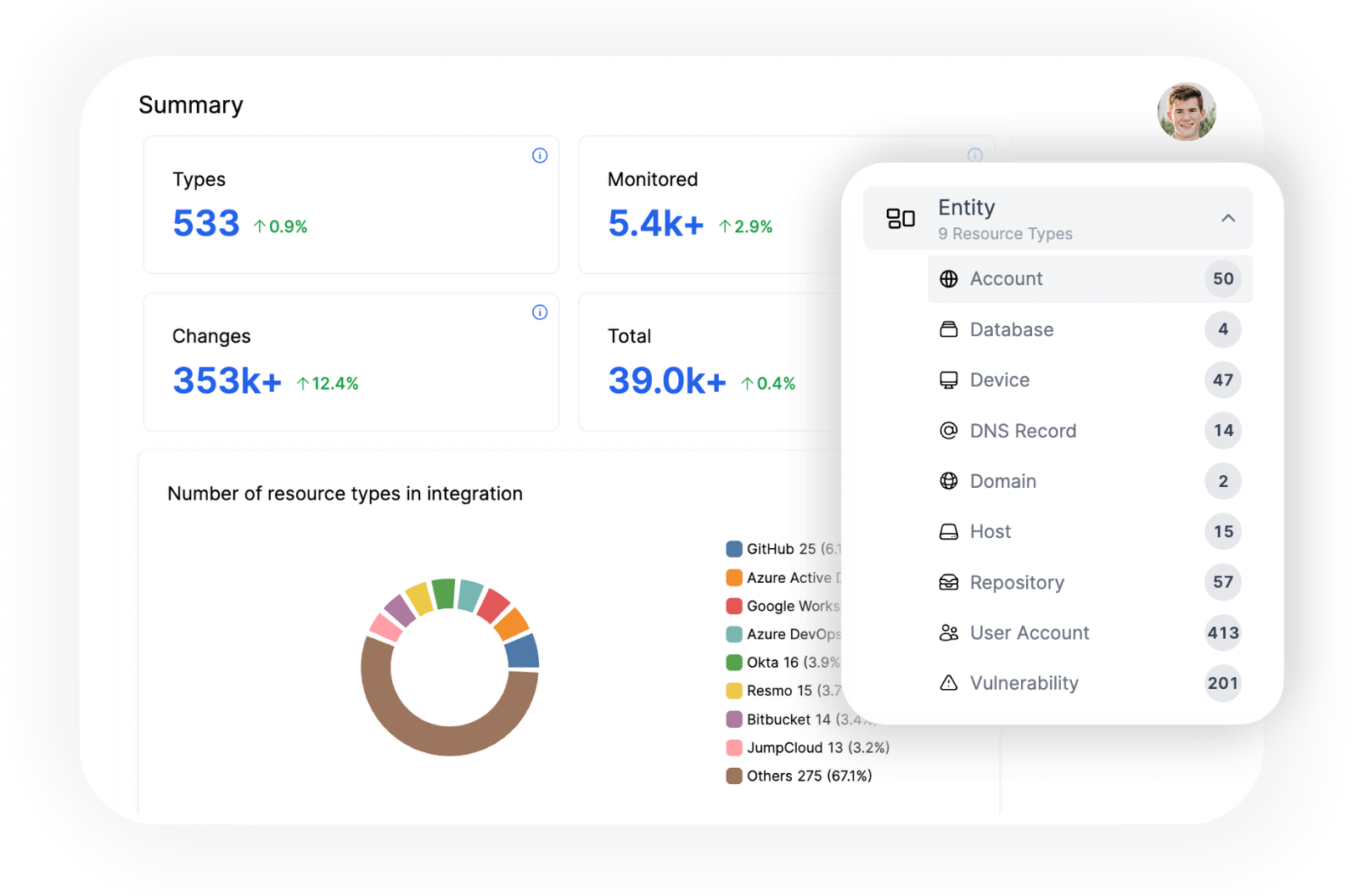
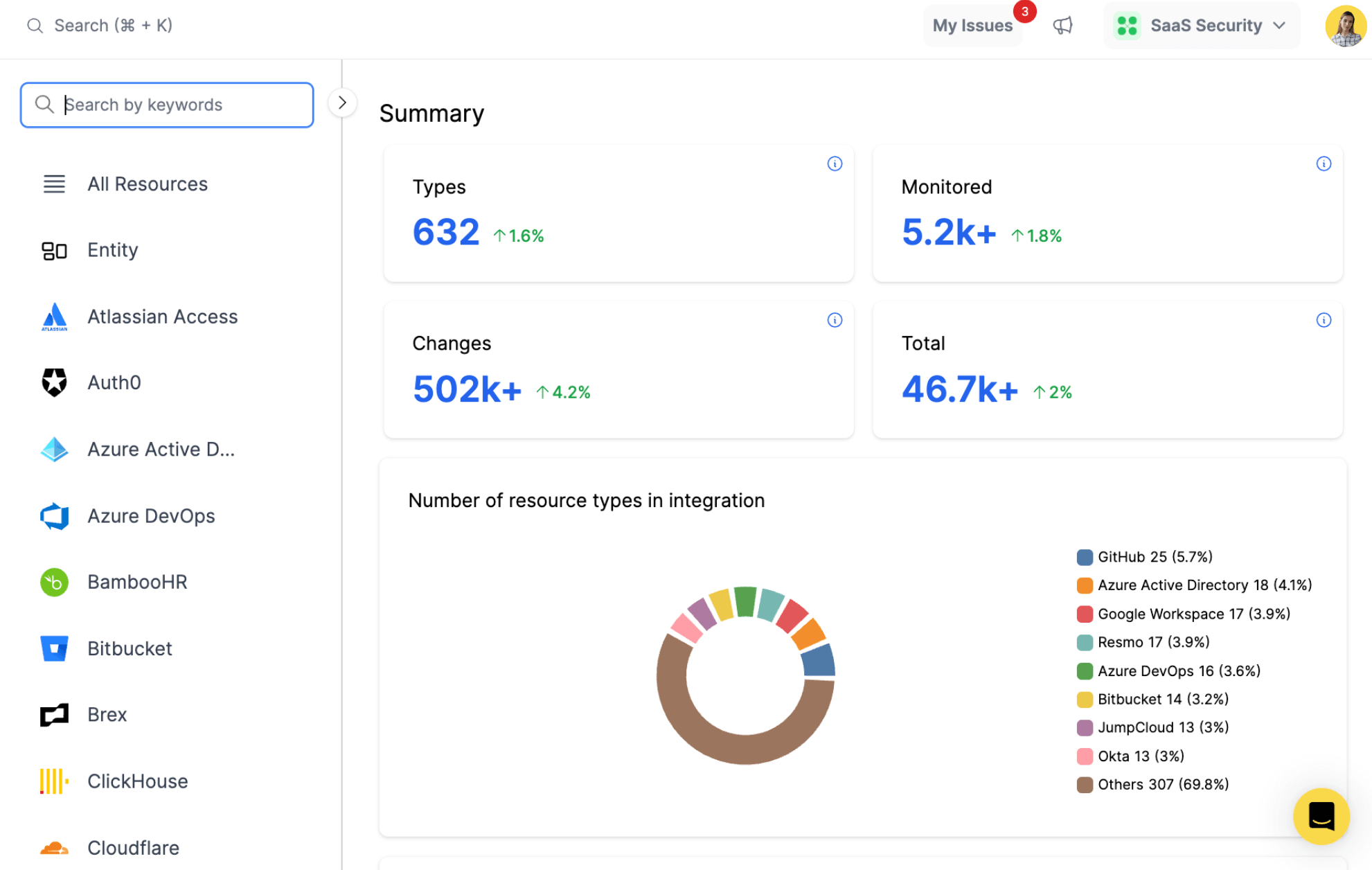
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- User
- User Authenticator
- User Role
- User Permission
- User Password
Get MonoSign Security Insights with Resmo
MonoSign is an Identity and Access Management (IAM) application with a built-in RADIUS Server. It enables comprehensive user authentication, authorization, role management, multi-step authentication (MFA), and single sign-on operations. Users first create an application to authenticate with MonoSign via its RADIUS Server.
Resmo's integration with MonoSign can provide detailed insights into user management, including user details, password strength, permission timelines, and role priorities. This information can support organizations in strengthening their access controls, improving password security, and effectively managing user roles and permissions, all leading to a more secure and efficient use of MonoSign's IAM capabilities.
Key features:
- Identify the details of each user, including their associated applications, groups, and permissions.
- Count the number of user passwords in the system, and determine their strength, usage count, and fail count.
- Find users with specific permissions, and understand when these permissions start and end.
- Determine the authenticators and roles associated with each user, and understand their priorities and states.
Secure your growth. Know what is happening on SaaS and Cloud.









