Collect and Analyze Data from CrowdStrike

Optimize Resource Management
Enhance visibility and control over your CrowdStrike environment. Track and manage user roles, host configurations, and policy settings. Maintain a strong cybersecurity infrastructure and prevent unauthorized access.
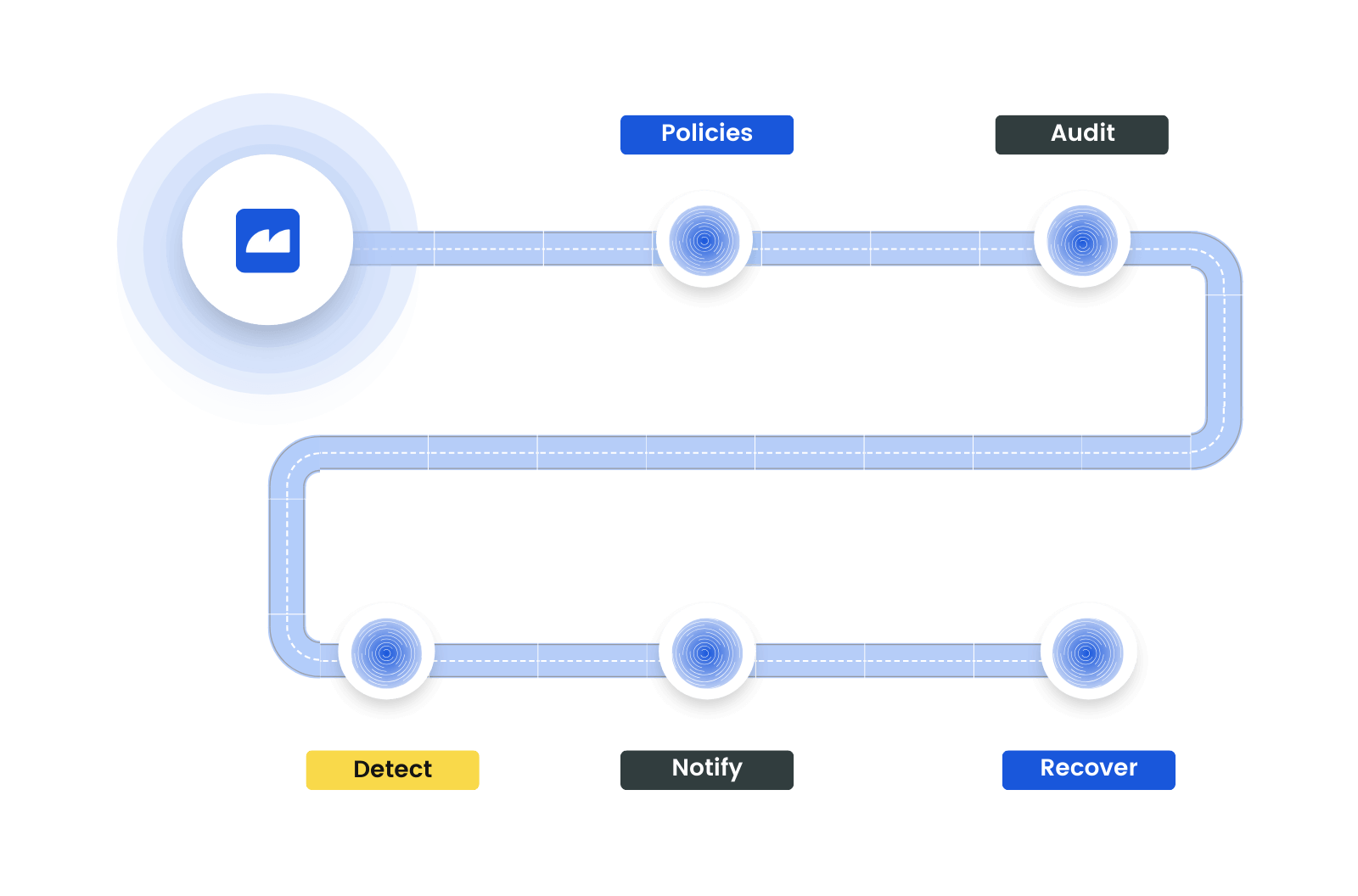
Enforce Custom Security Policies
Utilize Resmo's SQL queries to create and enforce tailored security policies. Analyze user permissions, host group memberships, and policy details to ensure your cybersecurity measures align with specific organizational needs and compliance standards.
✔︎ Custom and built-in policies
✔︎ Automated security audits
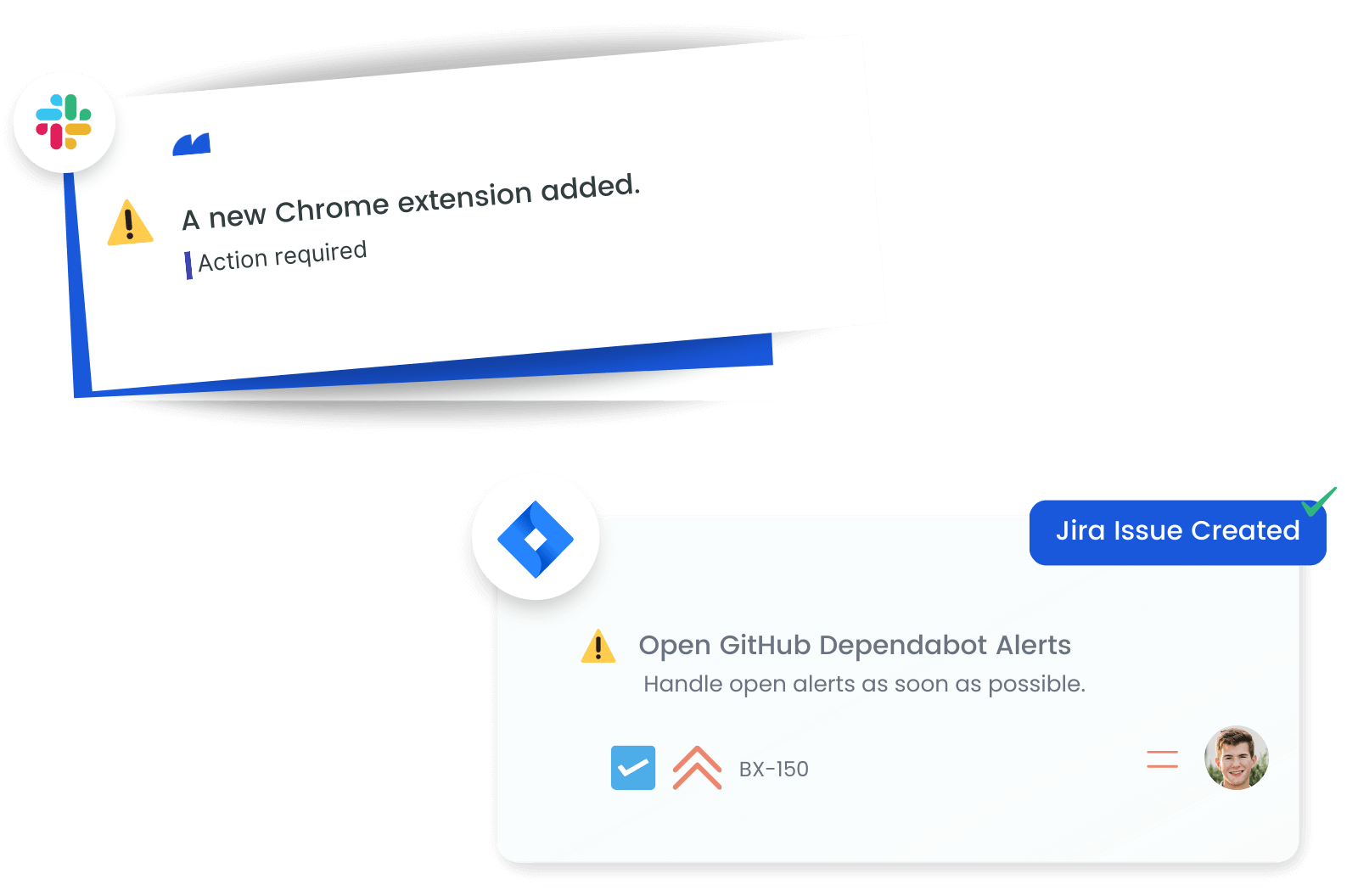
Receive Alerts on Critical Changes
Set up change alerts to stay ahead of crucial security modifications within your CrowdStrike environment. Immediate notifications on user, policy, and host changes enable rapid response, preventing security vulnerabilities.
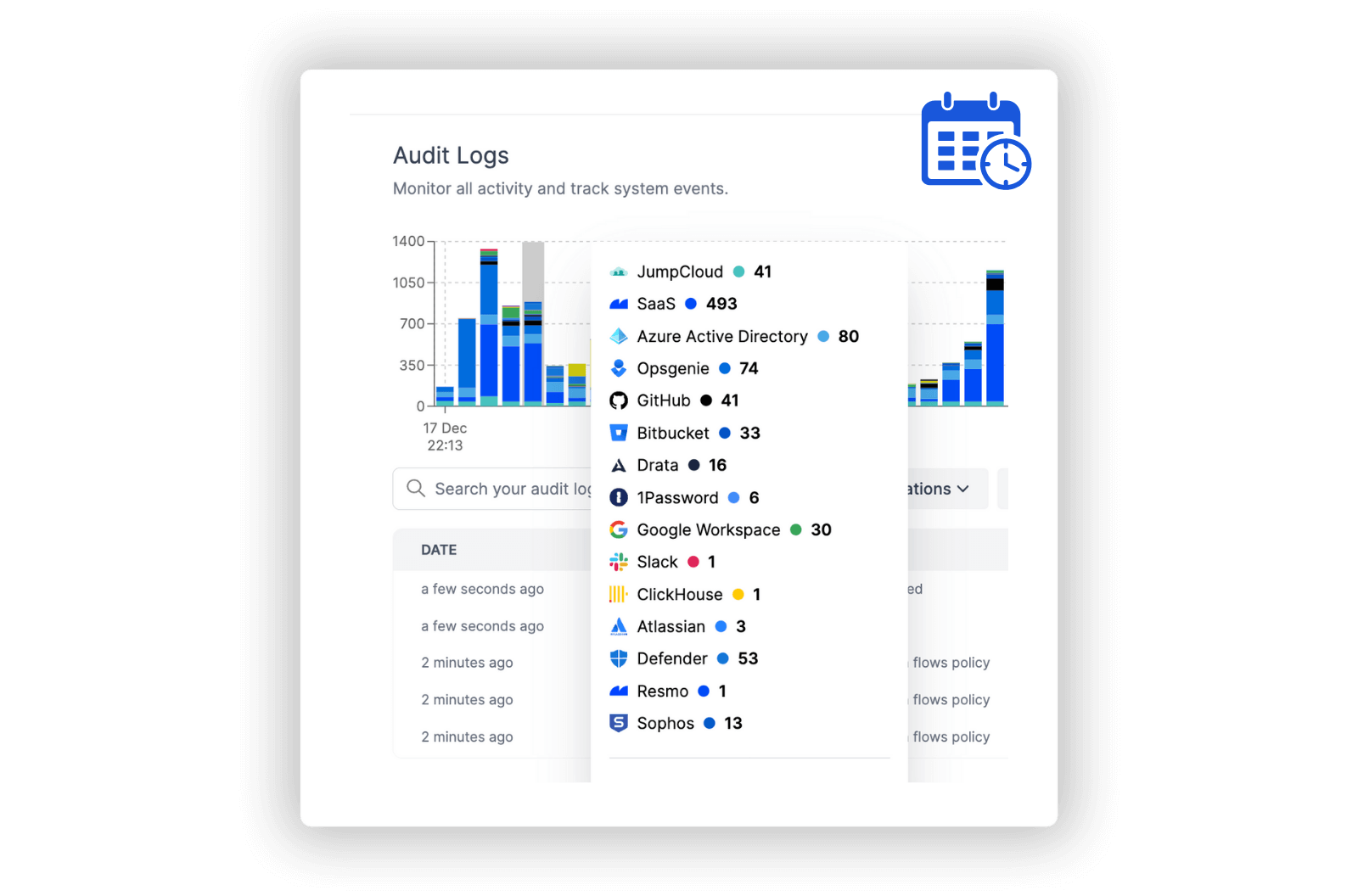
Accelerate Incident Investigations
Utilize audit logs to track and review all significant activities and events within CrowdStrike. Monitoring detections, policy updates, and sensor changes through these logs provides deep insights, enabling continuous refinement of your cybersecurity strategies and practices.
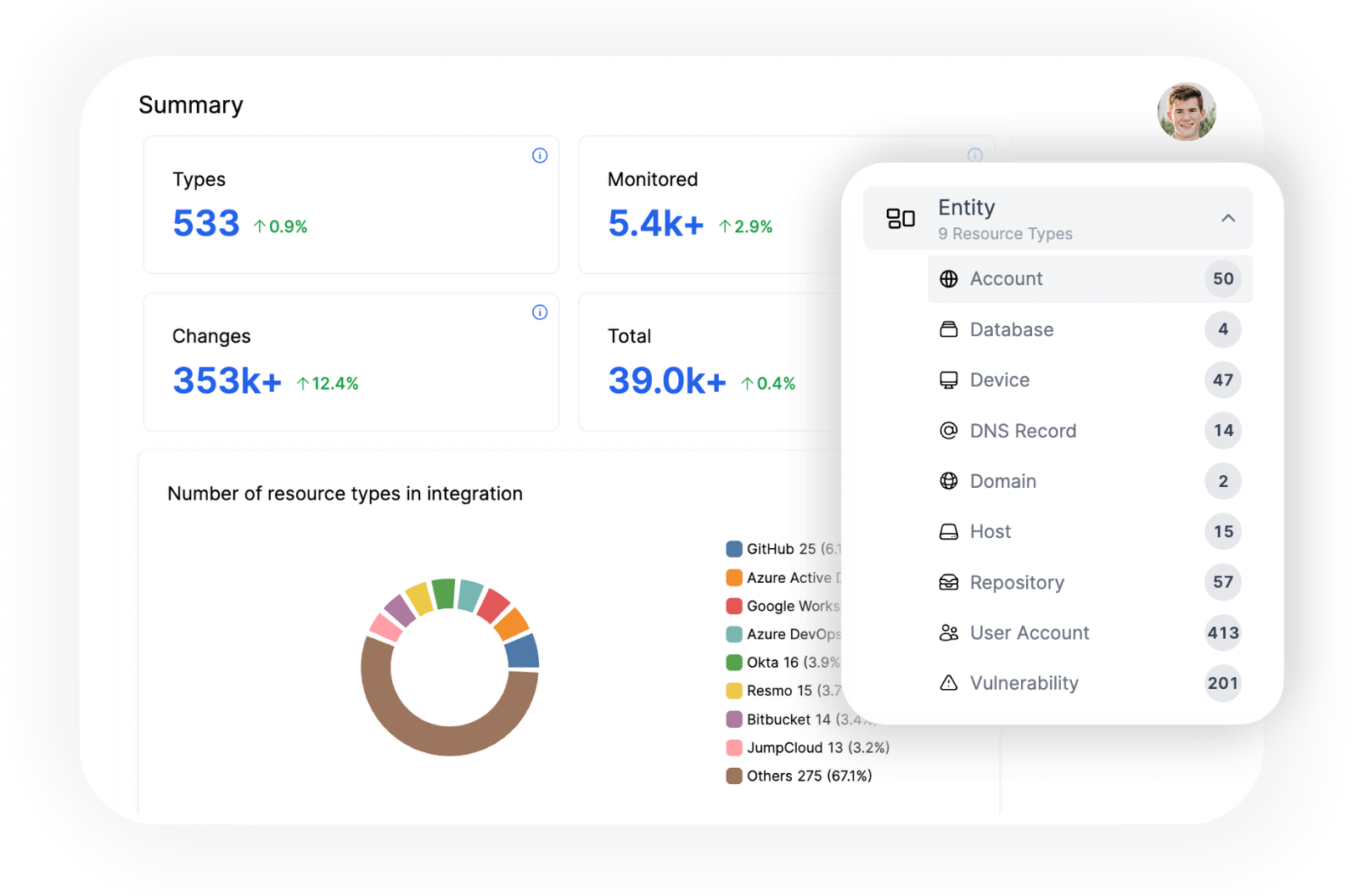
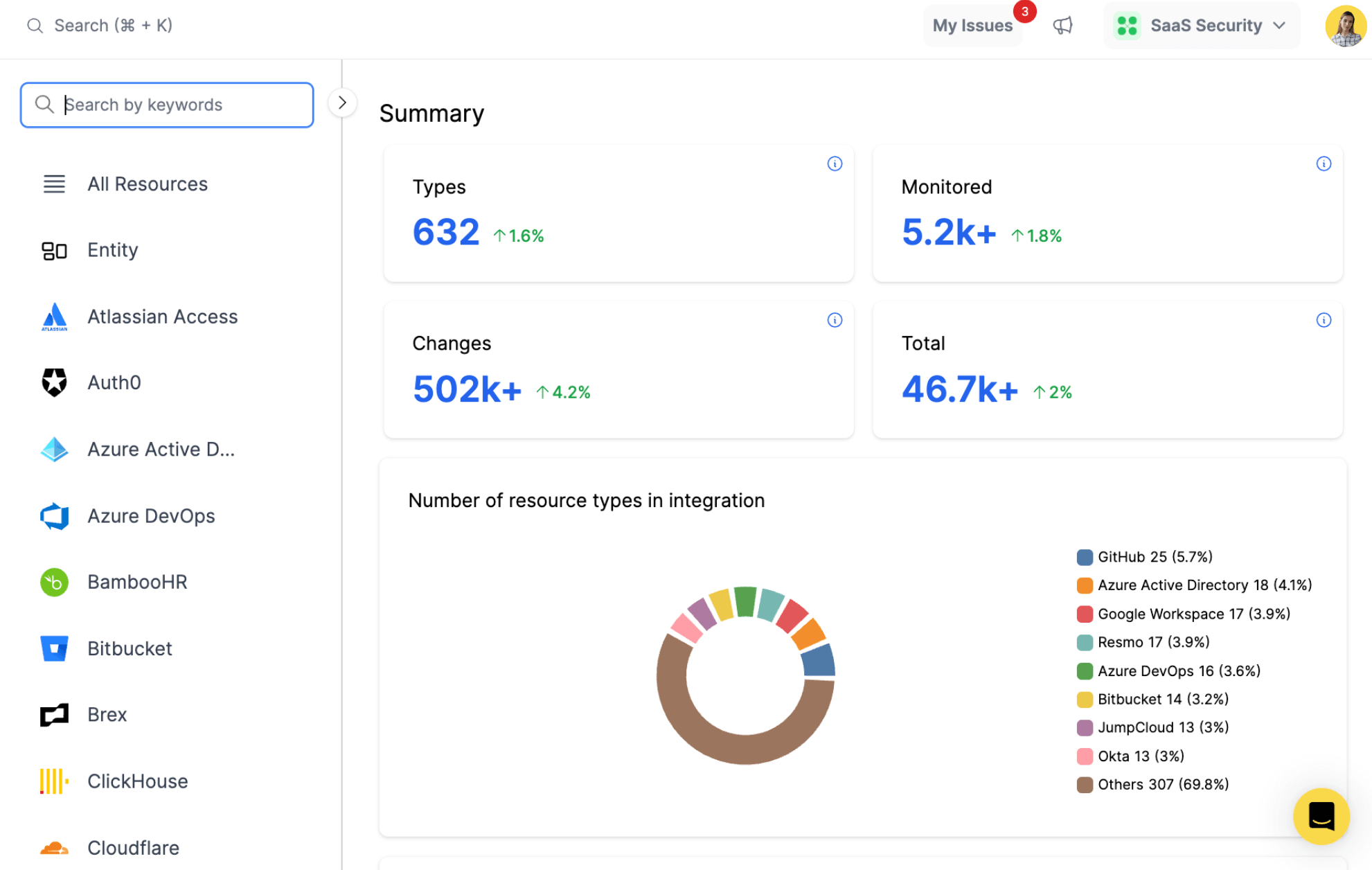
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- Detection
- Device Control Policy
- Firewall Policy
- Host
- Host Group
- Prevention Policy
- Response Policy
- Sensor
- Sensor Update Policy
- User
- User Role
Get Security Insights for CrowdStrike Resources
CrowdStrike is a cybersecurity technology company that provides cloud-native endpoint security. Its platform offers threat intelligence, endpoint protection, and cyber attack response services to detect and prevent breaches.
Resmo's integration with CrowdStrike facilitates an unparalleled understanding of your cybersecurity landscape. You gain clarity on the distribution of roles and permissions, allowing for better compliance management and security governance.
Key features:
- Identify users with specific roles and permissions within the CrowdStrike platform
- Enumerate system hosts, detailing their configurations, policies, and group memberships
- Analyze details of device control, firewall, prevention, response, and sensor update policies
- Track the number of detections, their associated behaviors, severity levels, and statuses
- Assess the configurations of sensors including their versions, file types, and associated platforms
Secure your growth. Know what is happening on SaaS and Cloud.









