Query, monitor, automate, repeat

Optimize Infrastructure Monitoring
Enhance your infrastructure oversight with insights from Datadog's monitoring and analytics data. Analyze user access, API key usage, and AWS integrations to refine your monitoring strategies.
✔︎ Streamline monitoring configurations for improved infrastructure oversight
✔︎ Identify and mitigate potential security risks in monitoring setups
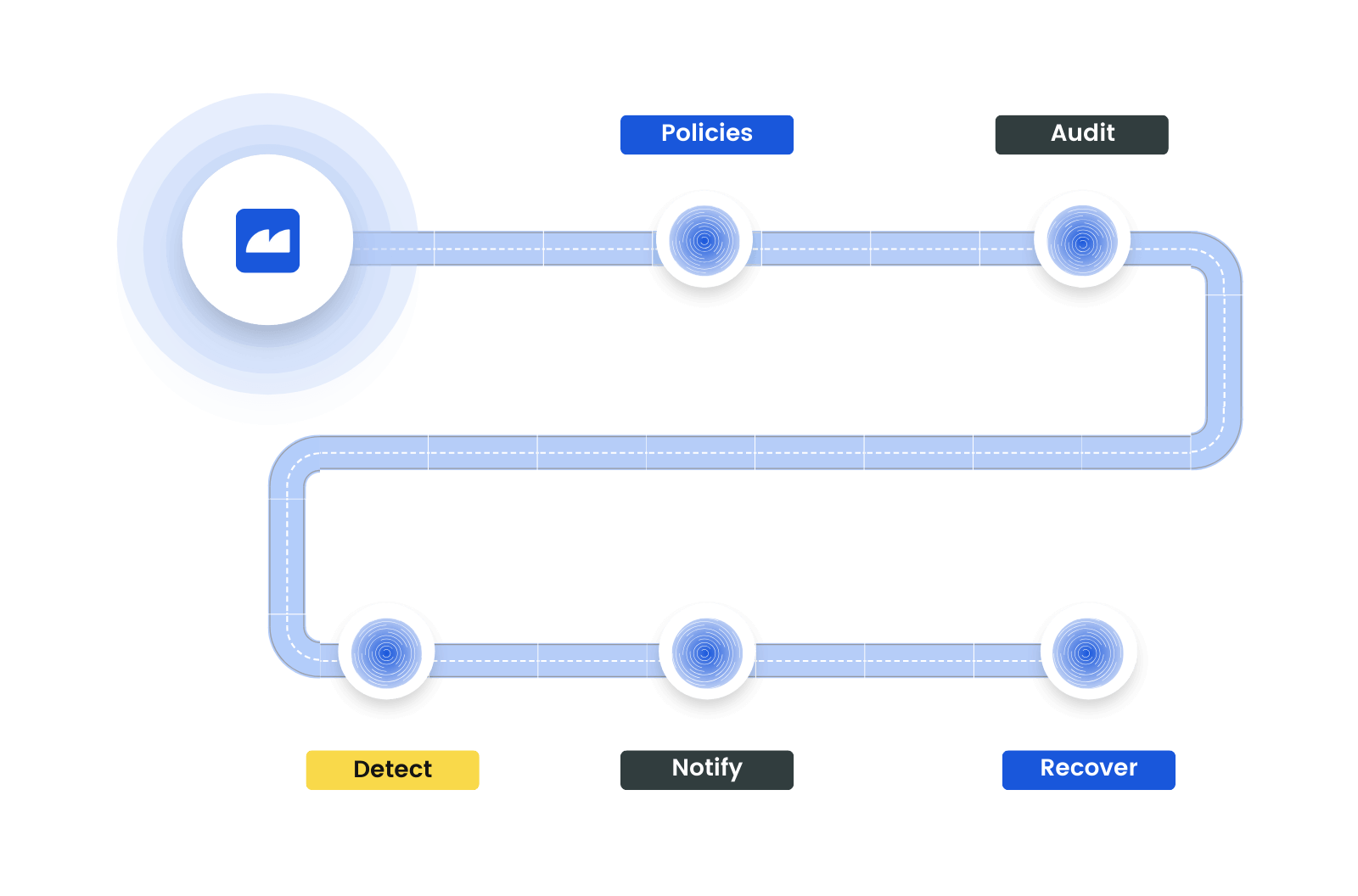
Strengthen Analytics and Alerting Practices
Leverage Resmo to ensure your Datadog configurations align with best practices in analytics and alerting. Monitor the setup and state of monitors, as well as organizational settings like SAML configurations, to maintain a high-performing, secure analytics environment.
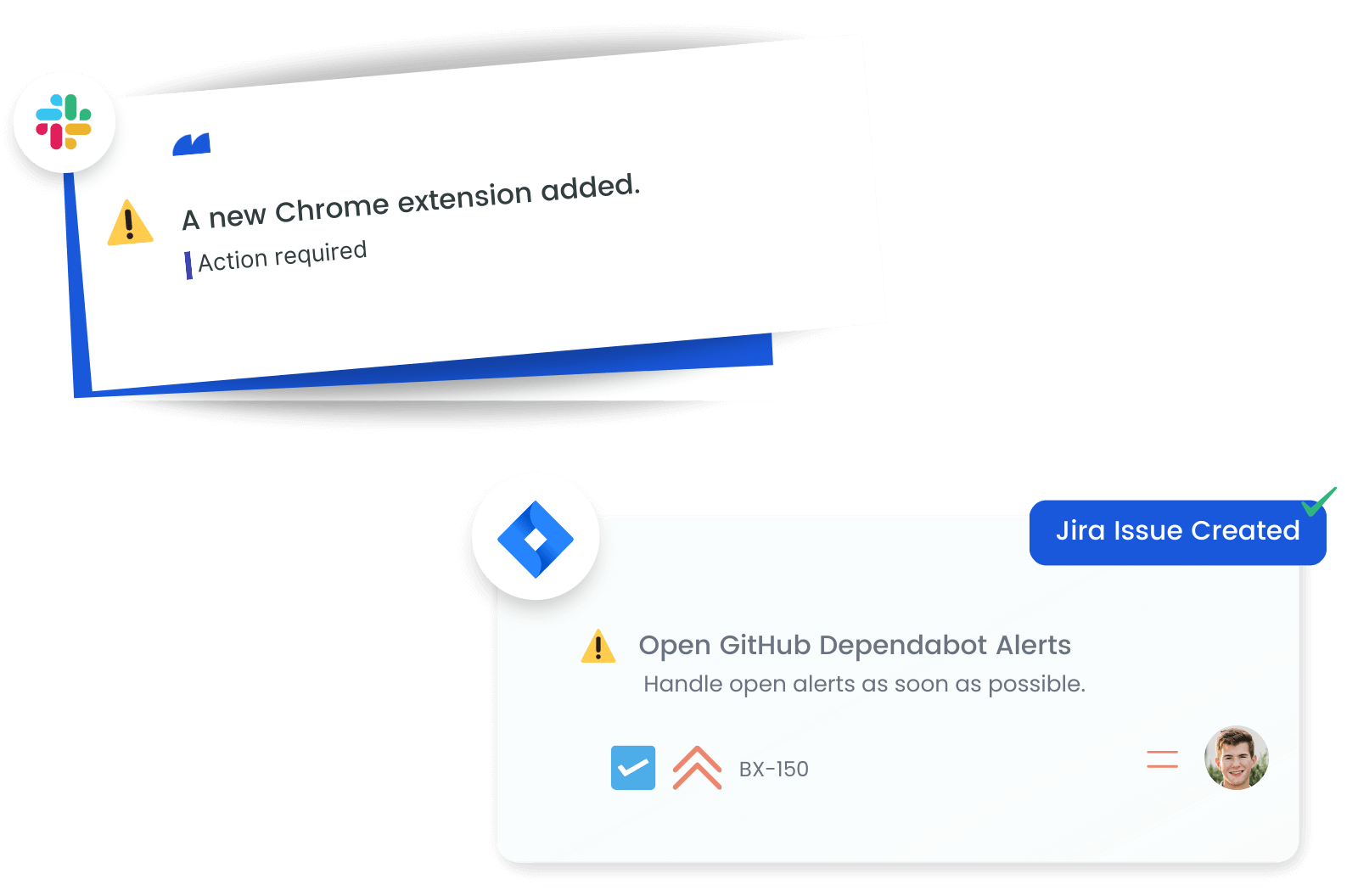
Stay Informed with Real-Time Configuration Alerts
Receive timely alerts on critical changes within your Datadog environment. Immediate notifications about updates to users, API keys, and monitors enable swift responses, ensuring your monitoring and analytics systems remain secure and effective.
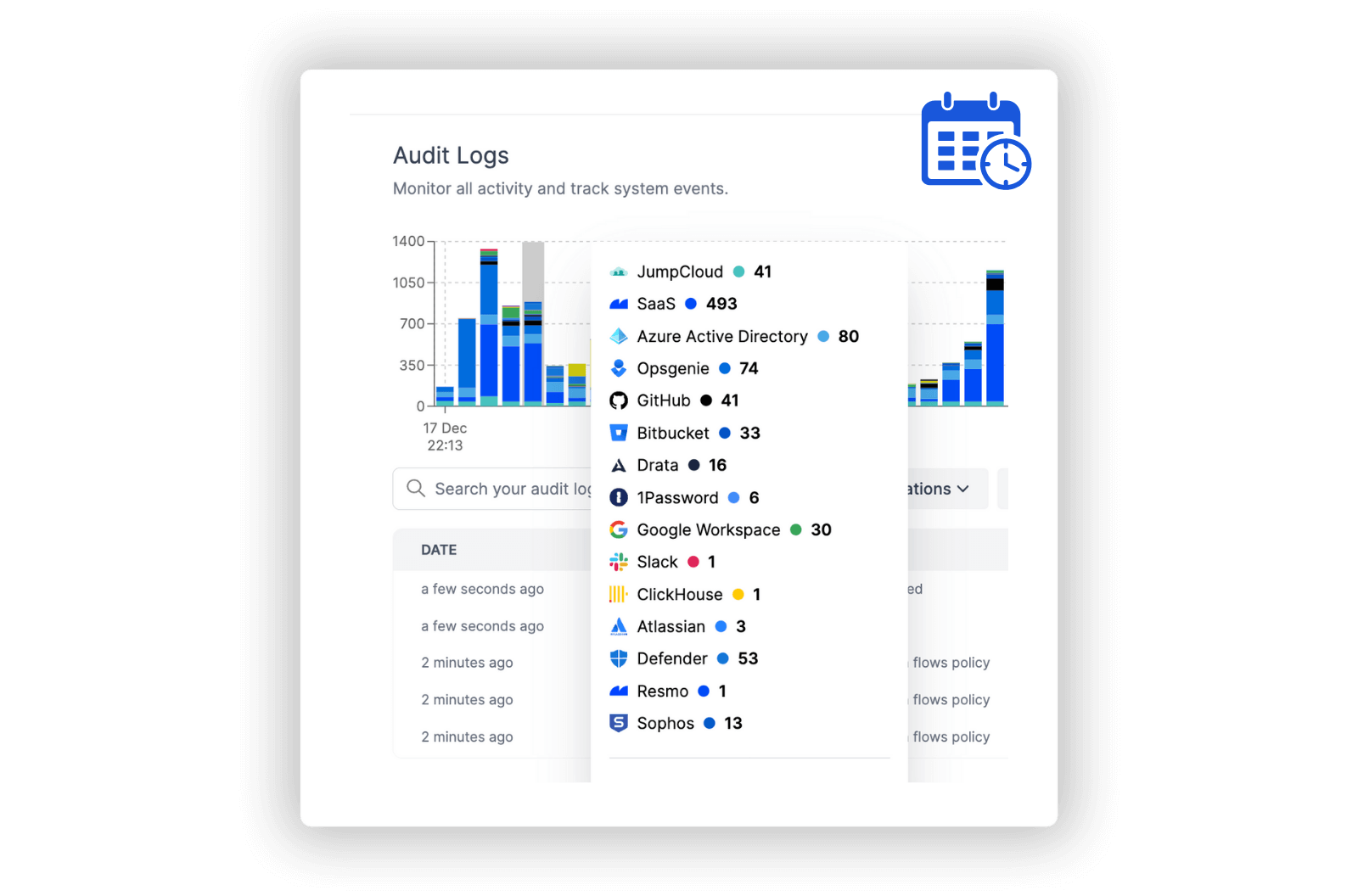
Accelerate Change or Misconfiguration Investigations
Access in-depth audit logs for a detailed analysis of Datadog activities. Review changes in AWS integrations, organizational settings, and user permissions to enhance your understanding of the monitoring environment, driving improvements in security and operational strategies.
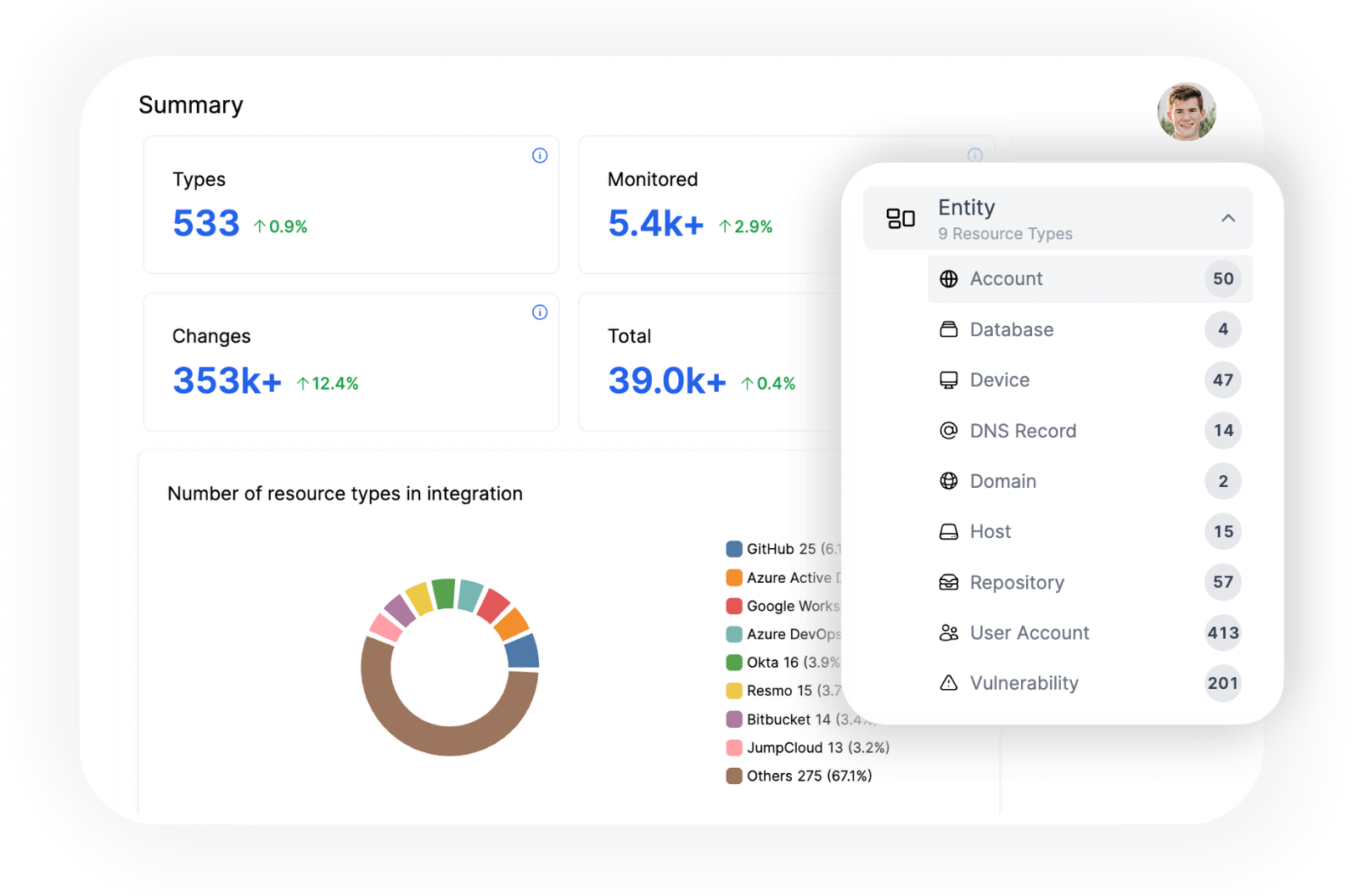
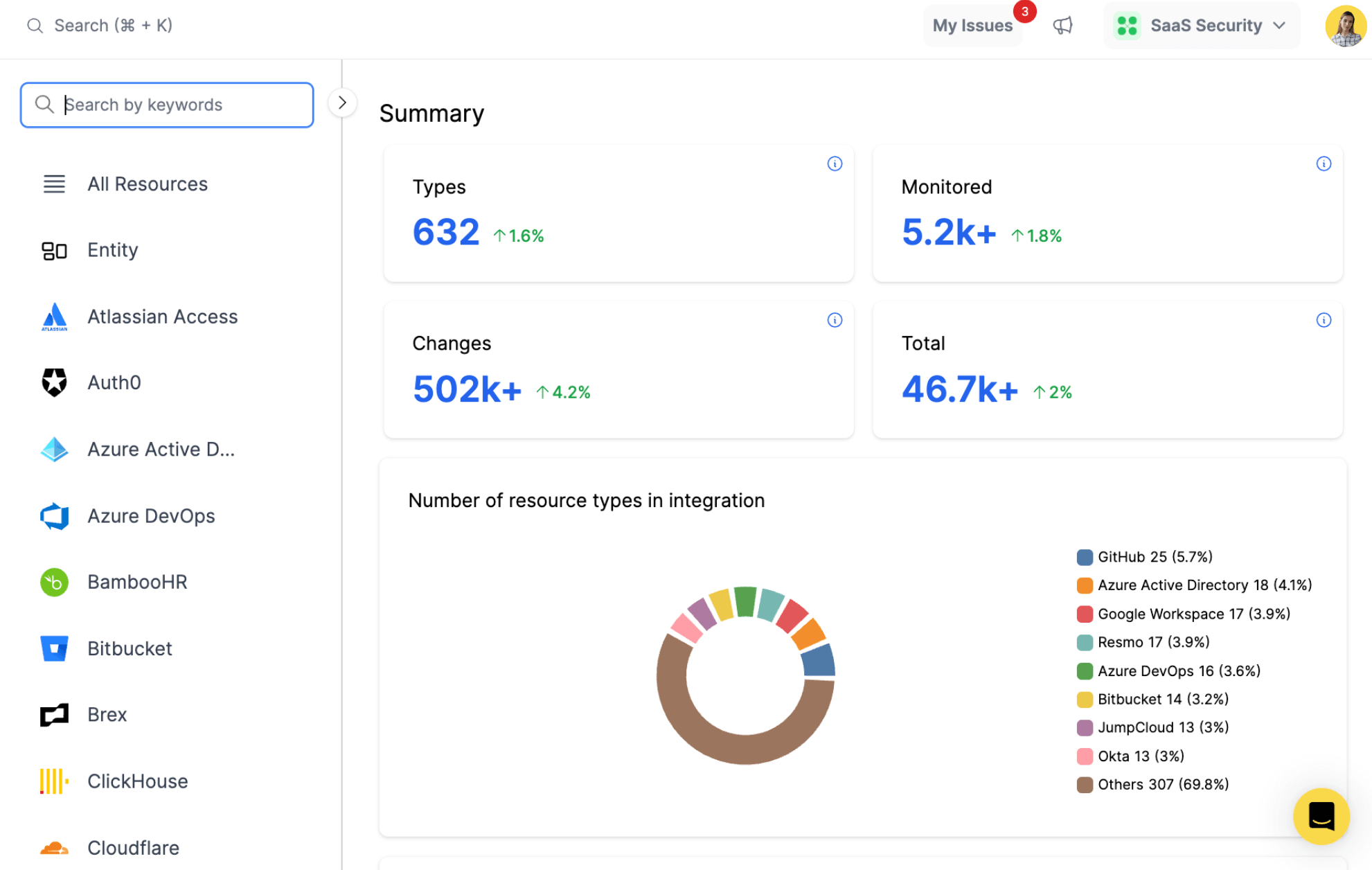
Explore all resources from a unified view.
resources
All key resources. Collected in near real time.
- API Key
- App Key
- AWS Integration
- Monitor
- Organization
- Permission
- Role
- User
Datadog Integration with Resmo
Datadog is a SaaS-based monitoring, security, and analytics platform that helps companies improve observability of their infrastructure and applications. It integrates and automates infrastructure monitoring, application performance monitoring, and log management to provide unified, real-time observability of an organization's entire technology stack.
Resmo's integration with Datadog offers you an enhanced understanding of your infrastructure monitoring landscape. It helps monitor users, their access permissions, and API keys, ensuring optimal security governance.
Key features:
- Identify users with access to specific resources and details about their permissions and roles
- Track the number of API and application keys in use, along with details about their creation and modification
- Provide detailed information about AWS integrations, including access keys, account IDs, and enabled features
- Analyze the number of configured monitors and their settings, priorities, and overall states
- Provide comprehensive information about organization settings, including billing and subscription types, SAML configurations, and public and private sharing options
Secure your growth. Know what is happening on SaaS and Cloud.









