
What is Shadow IT? Definition & Examples
One of the last things you'd think about when you go on vacation is whether your employer's network will still be intact upon your return. But this is a concern for IT staff: when non-IT users install an unapproved app or service, the potential risks are not under their control.
They can't ensure security mechanisms are in place, and they can't provide technical support. If Shadow IT goes south, the blame will fall on IT regardless. Whether the use of Shadow IT is intentional or not, it accompanies increased risks of data breaches, theft, potential compliance violations, and remediation costs.
This article will help you understand the definition of Shadow IT, risks that come with it, and how you can avoid it.
Shadow IT definition
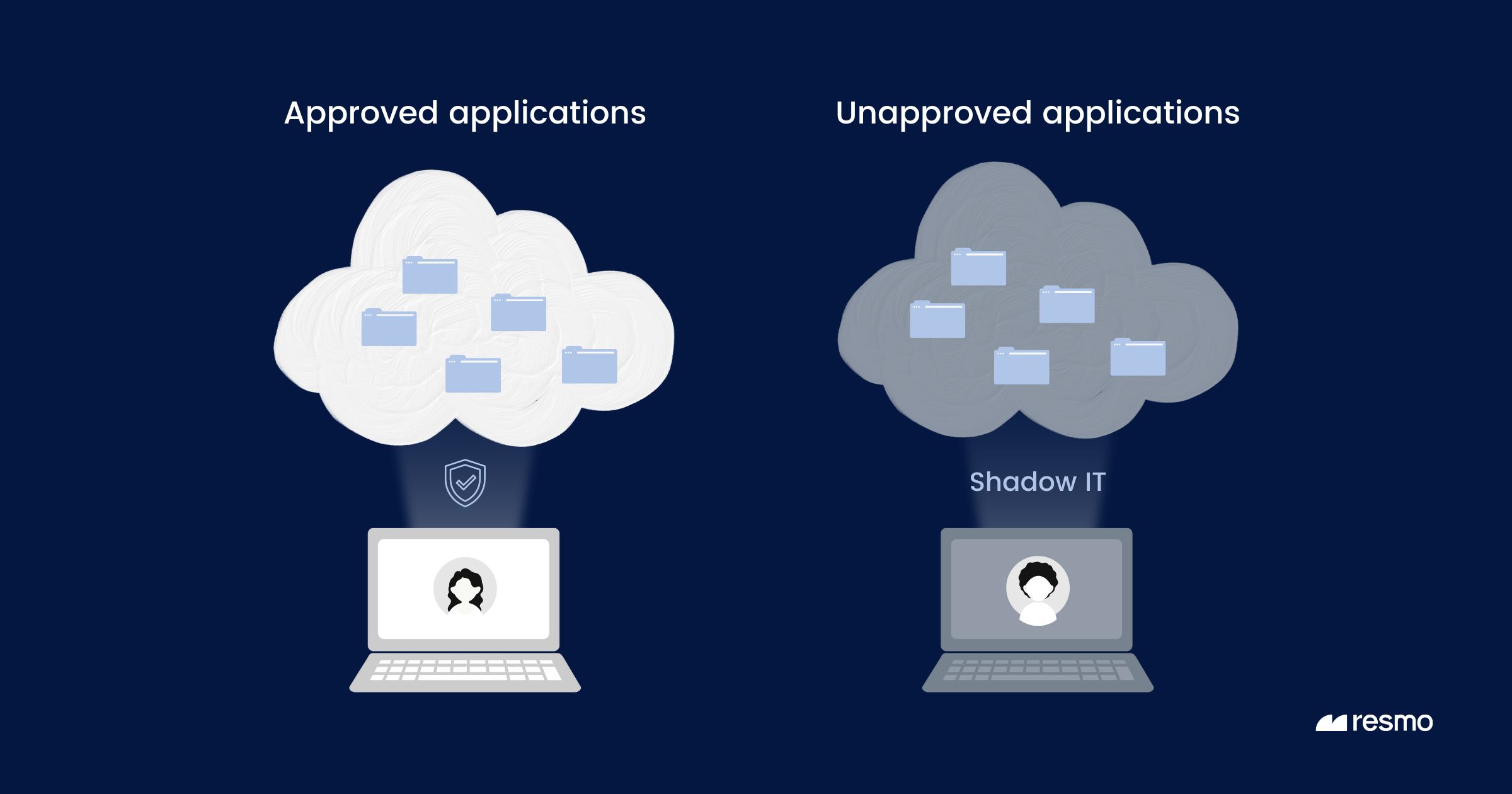
Shadow IT is the term used to describe information technology systems, solutions, and practices that are deployed and utilized within an organization without the explicit knowledge or approval of the IT department. It can range from unauthorized hardware devices and software installations to cloud-based services. While often adopted by employees to improve productivity or fill gaps in provided tools, shadow IT brings with it inherent risks, including security vulnerabilities, compliance issues, and potential data mismanagement.
Shadow IT can lurk in an organization's IT systems in many ways, but typically it occurs in two ways:
- Using unapproved tools, applications, or services to access, store, or share corporate data: For example, if an organization has approved Google Workspace for file sharing, but an employee chooses to share a corporate file using Dropbox, that employee can introduce Shadow IT into the company.
- Accessing approved tools, applications, or services in an unauthorized manner: For instance, if a company has exclusively approved the use of Google Workspace with a work email, an employee using a personal account to access the company workspace can cause shadow IT.
Shadow IT can happen for several reasons—from the fact that some employees don't feel like they have any control over their work environment to the fact that some employees just don't know how to get what they need from the system they're using.
Here are some reasons why shadow IT emerges:
- Speed: Business departments may feel that IT processes are too slow, so they seek out their own solutions to meet immediate needs.
- Simplicity: Non-IT departments might find third-party solutions more user-friendly than internal IT offerings.
- Lack of Understanding: Sometimes, business units might not be aware that an internal solution exists or they might not understand the processes required to obtain IT services.
What are the different aspects of Shadow IT?
Shadow IT encompasses all IT-related actions and acquisitions that bypass the formal IT department. These can include:
- Physical devices: such as servers, desktops, laptops, tablets, and mobile phones
- Packaged software
- Cloud services: like software as a service (SaaS), infrastructure as a service (IaaS), and platform as a service (PaaS).
What is a Shadow IT application?
A Shadow IT application refers to any software or application that is procured, deployed, and utilized within an organization without the explicit knowledge or approval of the IT department. This can include:
- Software installed on a workstation: This could be a simple tool or utility that a user installs on their computer without informing IT, possibly because it helps them perform their job more efficiently or because they're familiar with it from previous experience.
- Cloud-based applications: With the rise of Software as a Service (SaaS) offerings, many departments or individual users might subscribe to online services or platforms without routing the purchase or the usage through IT. Examples might include collaboration tools such as Figma, Google Drive, and Trello, project management platforms, or even specialized business apps.
- Mobile applications: Employees might download applications on their business-owned or personal mobile devices that they use for work purposes, which IT isn't aware of.
Shadow IT examples

Examples of Shadow IT include:
- Using productivity or workflow applications like Asana or Trello
- Using messaging or communication platforms like WhatsApp, Zoom, or similar apps for work-related conversations
- Creating cloud workloads with personal accounts or credentials
- Purchasing SaaS tools or other cloud services without the acknowledgment of the IT team
- Flash drives and HDDs
- Apple AirDrop and other Bluetooth services
While Shadow IT can increase employee productivity, it can also cause serious comebacks with security risks in data leaks, compliance violations, and more.
Why do employees use shadow IT?
The most prominent reason employees adopt shadow IT is to work more efficiently. Today's workforce is mostly remote. With the increased number of businesses transforming into remote work, more employees turned towards using Shadow IT.
According to a study, one or more services get exposed on the internet in 91% of devices in remote office networks.
For example, an employee can find a better application to share files than the IT-approved one and start using it without permission. Rapid growth and spread of cloud-based applications have also contributed to the increase in Shadow IT adoption. Gone are the days of the packaged software installed by the IT on employee devices; popular applications like Slack, Figma, and Dropbox are within a click's reach.
To sum it up, there are several reasons why Shadow IT happens:
- Employees don't know how to get access to the software they need.
- The software they want is blocked by security policies or other barriers.
- Employees don't want to use the approved software because it doesn't work well with their devices or processes.
- They just really like using those services better than what their company offers!
Shadow IT security risks and challenges
The primary risk of Shadow IT is that if IT staff isn't aware of a service or application, they can't check if it's secure. IT teams cannot track how services and tools in Shadow IT are used across their company, so they may have no idea how corporate data is being stored, accessed, or shared. Therefore, no matter how easier Shadow IT makes an employee's job, the potential drawback outweighs the convenience.

Shadow IT causes a lack of visibility and control over sensitive data in addition to the following risks:
1. Security risks
Sensitive data compromise or theft:
Shadow applications can be used to store or transfer sensitive organizational data. If they lack proper security controls, they could inadvertently expose confidential information, leading to data breaches.
In fact, an IBM report estimates that the global average total cost of data breaches is $4.35M.
Malware and viruses:
Unvetted software can introduce malware or other malicious entities into the organization.
Lack of encryption:
Data might be stored or transmitted without proper encryption, making it easier for unauthorized entities to access it.
2. Unintentional violation of compliance laws
For organizations that need to comply with data protection regulations like GDPR, being unable to track and control how their data is stored or processed may lead to compliance violations and heavy fines.
60% of organizations don't cover Shadow IT in their threat assessment, according to the Forbes and IBM's report.
3. Operational risks
- Integration Issues: Shadow IT solutions may not integrate well with other enterprise systems, leading to inefficiencies or inconsistencies.
- Increased Overhead: IT departments might waste resources dealing with problems arising from shadow IT or trying to integrate these solutions post-facto.
- Redundancy and Wasted Expenses: The organization may unknowingly pay for multiple tools that serve the same purpose.
4. Support and maintenance risks
- Lack of Expertise: IT teams may not be familiar with shadow IT solutions, making it challenging to provide support or troubleshoot issues when they arise.
- Discontinuation or Changes: External services or tools used without IT's knowledge could be discontinued, change their terms of service, or start charging, leading to disruptions.
How to prevent Shadow IT
Preventing Shadow IT involves a combination of technical controls, policies, and fostering a culture of open communication. Here are some steps organizations can take:
1. Educate users
Shadow IT often emerges from a lack of understanding about potential risks. Regular training sessions and workshops can enlighten employees about the dangers associated with using unauthorized technologies. By creating a well-informed workforce, you can reduce the allure of shortcuts and encourage adherence to official IT protocols. Interactive sessions, real-life examples, and consistent communication can reinforce the importance of this education.
2. Foster Open Communication
Encourage employees to openly discuss their technological needs with the IT department. By fostering an environment of trust and responsiveness, you reduce the likelihood of staff seeking external solutions. Regular feedback channels, such as town hall meetings or IT suggestion boxes, can provide insights into employee needs and potential areas of improvement for IT services.
3. Streamline IT Approvals
A bureaucratic and slow approval process can deter employees from following official channels. By optimizing and streamlining these processes, you can ensure that employees get the tools they need promptly, reducing the appeal of shadow IT. Implementing a tiered approval system or automating certain request processes can make this more efficient.
4. Conduct Regular Audits
Periodic checks on software, hardware, and network activities are crucial for detecting unauthorized tools and services. Utilizing automated monitoring solutions can help in early detection of shadow IT, ensuring timely intervention. Cloud Access Security Brokers (CASBs) are especially useful in controlling and monitoring cloud service usage, ensuring data security.
5. Implement Access Controls
Rigorous access controls ensure that only vetted devices and applications can connect to the company's network. Regularly updating and reviewing these controls prevents potential security breaches. A multi-factor authentication system and stringent password policies can further enhance security by restricting unauthorized access.
6. Whitelist Approved Applications
By maintaining a list of sanctioned applications, a.k.a. application whitelisting, and allowing only those to run, you can ensure software consistency and security across the organization. Regular updates to this list, in consultation with various departments, ensures that all employee needs are met while maintaining a secure IT environment.
7. Provide Unified IT Solutions
When the IT department offers comprehensive and up-to-date solutions, employees are less likely to seek alternatives. Understanding the diverse needs of various departments and tailoring solutions accordingly can preempt the inclination towards shadow IT. Collaboration tools, CRM systems, and project management software are common areas where unified solutions can be beneficial.
8. Deploy DLP Tools
Data Loss Prevention tools offer a proactive approach to monitor and control data transfers across the company network. By setting up alerts for suspicious transfers or unauthorized data access, the IT team can immediately address potential breaches. This not only curbs shadow IT but also offers a broader layer of data security.
9. Formulate Clear IT Policies
Well-defined IT policies provide a framework for acceptable technology use within the organization. By clearly communicating these policies and ensuring that all employees are aware of them, you can set clear boundaries. Regular updates and revisions of these policies keep them relevant and effective.
10. Manage Mobile Devices Proactively
With the rise of mobile device usage in workplaces, it's crucial to have systems like Mobile Device Management (MDM) or Enterprise Mobility Management (EMM) in place. These tools allow IT teams to control which applications can be installed on company devices, ensuring security and consistency. They also help in remotely managing and securing devices, which is especially useful for remote teams or in case of device loss.
11. Use a SaaS security tool
IT teams might not always catch unapproved SaaS applications. That's why the better solution can be automating the SaaS app discovery, risk detection, and remediation process with a SaaS security tool.
Shadow app discovery: Detect SaaS applications employees login with their business credentials such as OAuth logins with Google Workspace or Atlassian.
SaaS risk detection: Identify misconfigurations that might pose threat to an organization's security such as weak or repeated passwords.
Shadow IT FAQ
How does Shadow IT work?
Shadow IT increases the risks of data compromise by leaving your IT team unaware and without control. For example, an employee with access to your company Drive file can download and store it on their own cloud storage. This, in return, may lead to a data leak and serious security breaches depending on the compromised data.
What is an example of Shadow IT?
Some common examples of Shadow IT include the non-official use of cloud-based tools like Drive, Google Docs, Gmail, and Dropbox, as well as Bluetooth sharing tools like Apple Airdrop. For instance, a personal email account used to access a company file falls under shadow IT.
Why do people use shadow IT?
People typically use Shadow IT to boost their productivity and efficiency during work. With the growth of SaaS tools, there is a tool for any small task they might have. Since the official approval process of an IT department can take too long, employees turn towards Shadow IT.
What is the risk from network-accessed shadow IT applications?
Network-accessed shadow IT applications, which are used without IT department approval, pose significant risks to organizations. They can introduce security vulnerabilities, lead to data breaches due to inadequate safeguards, result in non-compliance with industry regulations, and potentially enable malware attacks or data loss.
Additionally, without IT oversight, there's reduced visibility into potential malicious activities, integration issues with existing systems, and strains on network resources, all of which can compromise both operational efficiency and corporate reputation.
What is the risk from OAuth-enabled shadow IT applications?
OAuth-enabled shadow IT applications pose distinct risks because they allow third-party access to user data without directly sharing credentials. Users might inadvertently grant these apps overly broad permissions, potentially leading to data breaches, account takeovers, or unauthorized actions on their behalf. Additionally, without IT oversight, there's a lack of visibility into which external applications have data access, and insecure token handling can result in token hijacking, further exposing sensitive data and accounts.
Bottom line
We hope this blog has given you a better idea of what Shadow IT is, why it happens, and how to prevent Shadow IT, if possible. While some forms of Shadow IT can hurt your company's security and cause problems with your policies, successful implementations of Shadow IT can have some benefits for the people using it.
To put this in perspective, know that a substantial portion of all successful software solutions is products of Shadow IT. Ultimately, you will still need to be able to trust your users. But by being aware of Shadow IT and its risks as well as keeping employees educated on it, you can see it for what it is and take action to prevent it from causing technical problems for your company.
Next on your reading list:







